Preventing Data Leakage in scFM Benchmarking: A Guide for Robust and Reproducible Drug Discovery
This article addresses the critical challenge of data leakage in single-cell force microscopy (scFM) benchmarking for drug discovery.
Preventing Data Leakage in scFM Benchmarking: A Guide for Robust and Reproducible Drug Discovery
Abstract
This article addresses the critical challenge of data leakage in single-cell force microscopy (scFM) benchmarking for drug discovery. As machine learning becomes integral to analyzing compound-protein interactions, ensuring unbiased and reproducible benchmarks is paramount. We explore the foundational causes and consequences of data leakage, drawing parallels from computational chemistry benchmarks. The content provides methodological guidance for constructing leakage-free datasets, troubleshooting common pitfalls in experimental design, and establishing rigorous validation protocols. Aimed at researchers and drug development professionals, this guide synthesizes best practices to safeguard the integrity of predictive models in biomedical research, fostering trust in AI-driven discovery.
Understanding Data Leakage: Why It Undermines scFM Benchmarking in Biomedical Research
FAQs: Data Leakage in Computational Drug Discovery
What is data leakage in the context of machine learning for drug discovery? Data leakage occurs when information from outside the training dataset is used to create a machine learning model. This leads to overly optimistic performance estimates during testing because the model has, in effect, already "seen" the test data. When this happens, the model memorizes the training data instead of learning generalizable properties, resulting in poor performance when applied to real-world, out-of-distribution data [1].
Why is data leakage a critical problem for drug discovery and scFM benchmarking? Data leakage compromises the reliability of model evaluations. In fields like molecular property prediction or single-cell perturbation effect prediction, a model that has experienced data leakage will fail to generalize to new, unseen molecules or cellular states. For example, in single-cell foundation model (scFM) benchmarking, PertEval-scFM found that models offered limited improvement over baselines in zero-shot settings, particularly under distribution shift, highlighting the need for rigorous, leakage-free evaluation to assess true model capability [2] [3].
How can data leakage lead to the exposure of proprietary chemical structures? Publishing neural networks trained on confidential datasets poses a significant privacy risk. Adversaries can use Membership Inference Attacks (MIAs) to determine whether a specific molecule was part of the model's training data. In a black-box setting, similar to making models available as a web service, these attacks can successfully identify training data molecules, thereby exposing proprietary chemical structures. This risk is especially high for molecules from minority classes and for models trained on smaller datasets [4].
What are the common technical causes of data leakage in biomedical ML?
- Inappropriate Data Splitting: Randomly splitting datasets that contain highly similar data points (e.g., molecules with similar structures or proteins from the same family) can lead to leakage. If similar samples are in both training and test sets, the model is not truly tested on novel data [1].
- Feature Selection Before Splitting: Performing feature selection or normalization on the entire dataset before splitting it can allow information from the test set to influence the training process.
- Model Sharing: As explored in the "Publishing neural networks in drug discovery might compromise training data privacy" study, the act of sharing a trained model itself can be a source of leakage, as the model's outputs can be queried to infer the training data [4].
Troubleshooting Guides
Issue: Inflated Model Performance During Training with a Sharp Drop on Real-World Data
This is a classic symptom of data leakage, where your model performs exceptionally well in validation but fails in practice.
Investigation and Resolution Protocol:
Audit Your Data Splitting Strategy:
- Action: Verify that your data splitting method accounts for the inherent similarities in your biological data. For molecular data, this means ensuring that structurally similar compounds are not spread across training and test sets. For protein-related tasks, ensure that proteins with high sequence homology are not in different splits.
- Tool: Use a tool like DataSAIL to perform similarity-aware data splitting. DataSAIL formulates the splitting problem to minimize information leakage as a combinatorial optimization problem, ensuring that your test set is truly out-of-distribution relative to your training set [1].
- Visual Workflow:
Check for Preprocessing Errors:
- Action: Confirm that all preprocessing steps (e.g., normalization, imputation, feature selection) were fit only on the training data and then applied to the validation and test sets. Any step that uses global dataset statistics contaminates the training process.
Evaluate Privacy Risks Before Model Sharing:
- Action: If you plan to publish your model, assess its vulnerability to privacy attacks.
- Tool: Implement a framework like the one provided in the cited study (available at
https://github.com/FabianKruger/molprivacy) to run Membership Inference Attacks against your own model [4]. - Mitigation: Consider using molecular representations that are less susceptible to leakage. The same study found that representing molecules as graphs and using message-passing neural networks resulted in the least information leakage across all evaluated datasets [4].
Issue: Membership Inference Attacks Successfully Identify Training Set Molecules
If your proprietary model is found to be leaking information about its training data, take these steps to understand and mitigate the risk.
Investigation and Resolution Protocol:
Quantify the Risk:
- Action: Use Likelihood Ratio Attacks (LiRA) and Robust Membership Inference Attacks (RMIA) to measure the True Positive Rate (TPR) at a very low False Positive Rate (FPR), such as 0 or 0.001. This will tell you how many of your training molecules can be confidently identified [4].
- Interpretation: The table below summarizes the privacy risks found across different molecular property prediction tasks, showing that smaller datasets are at higher risk [4].
Table 1: Privacy Risk from Membership Inference Attacks
Dataset Training Set Size Key Finding Blood-Brain Barrier (BBB) 859 molecules Median TPR between 0.01-0.03 at FPR=0 (9-26 molecules identified) Ames Mutagenicity 3,264 molecules Significantly higher TPR than random guessing DNA Encoded Library (DEL) 48,837 molecules TPRs decreased with larger dataset size; one attack performed significantly better hERG Inhibition 137,853 molecules TPRs decreased with larger dataset size; one attack performed significantly better Choose a Safer Model Architecture:
- Action: Transition from using simpler molecular representations (like fingerprints or SMILES) to graph-based representations with message-passing neural networks.
- Evidence: Research shows that the graph representation consistently had the lowest TPRs across all datasets and attacks, with a median TPR that was on average 66% ± 6% lower than other representations. For larger datasets, it was the only representation that sometimes prevented attackers from identifying more molecules than by random guessing [4].
Understand Attacker Advantages:
- Action: Be aware that combining different MIAs (LiRA and RMIA) can identify a wider range of training data molecules than using a single attack method, as they do not always identify the same molecules [4].
Experimental Protocols for Data Leakage Assessment
Protocol: Assessing Model Privacy with Membership Inference Attacks (MIA)
Objective: To evaluate the risk that a trained machine learning model will leak information about its proprietary training data.
Methodology:
- Model Training: Train your target model (e.g., a neural network for molecular property prediction) on your confidential dataset.
- Attack Setup: In a black-box setting, assume the adversary has access to the model's output logits (e.g., via a web service). The adversary does not need access to the model's internal weights.
- Execute Attacks:
- Apply two state-of-the-art attacks: the Likelihood Ratio Attack (LiRA) and the Robust Membership Inference Attack (RMIA) [4].
- The attacks query the model with samples from the training set and from a hold-out set not seen during training.
- Evaluation Metric: Calculate the True Positive Rate (TPR) at a fixed, low False Positive Rate (FPR), such as 0 or 0.001. A TPR significantly above the random guessing baseline indicates a successful attack and information leakage [4].
Protocol: Creating Leakage-Reduced Data Splits with DataSAIL
Objective: To split a dataset into training, validation, and test sets in a way that minimizes information leakage and enables a realistic evaluation of a model's performance on out-of-distribution data.
Methodology:
- Problem Formulation: DataSAIL treats data splitting as a combinatorial optimization problem that is NP-hard. It uses a scalable heuristic based on clustering and integer linear programming (ILP) to find a solution [1].
- Input: Provide your dataset and a similarity or distance measure for the data points (e.g., molecular similarity, protein sequence homology).
- Splitting Mode: Choose the appropriate splitting task. For drug-target interaction prediction (a 2D problem), use similarity-based two-dimensional splitting (S2) to ensure that neither similar drugs nor similar targets are shared between splits [1].
- Output: DataSAIL returns data splits where the similarity between data points in the training set and the test set is minimized, providing a more realistic and challenging benchmark for your models [1].
Table 2: DataSAIL Splitting Schemes for Different Data Types
| Data Type | Splitting Scheme | Description | Goal |
|---|---|---|---|
| 1D (e.g., Small Molecules) | Similarity-based (S1) | Splits data so that samples in the test set are dissimilar to those in the training set. | Prevents models from exploiting molecular similarity shortcuts. |
| 2D (e.g., Drug-Target Pairs) | Similarity-based (S2) | Splits data so that neither the drugs nor the targets in the test set are highly similar to those in the training set. | Forces the model to learn generalizable interaction rules, not rely on similarities in either dimension. |
The Scientist's Toolkit: Key Research Reagent Solutions
Table 3: Essential Computational Tools for Data Leakage Prevention
| Tool / Solution | Function | Relevance to Data Leakage |
|---|---|---|
| DataSAIL [1] | A Python package for computing similarity-aware data splits for 1D and 2D biomolecular data. | Prevents information leakage during the data splitting stage, the most common source of leakage. |
| MolPrivacy Framework [4] | A framework for assessing the privacy risks of classification models and molecular representations via Membership Inference Attacks. | Allows researchers to proactively test their models' vulnerability before publication. |
| Message-Passing Neural Networks (MPNN) [4] | A neural network architecture that operates directly on graph representations of molecules. | A safer architecture that demonstrates significantly less information leakage compared to models using other molecular representations. |
| PertEval-scFM Benchmark [2] [3] | A standardized framework for evaluating single-cell foundation models on perturbation effect prediction. | Provides a rigorous, standardized testing ground that helps identify model limitations and over-optimism potentially caused by data leakage. |
| Dark Web Scanning Tools [5] | Proactive security tools that search hacker forums and ransomware blogs for leaked data. | Protects the underlying training data from being stolen and used to attack models or compromise intellectual property. |
FAQs on Data Leakage in Computational Drug Discovery
Q1: What is data leakage in the context of compound activity prediction? Data leakage occurs when information from the test dataset inadvertently influences the training process of a model. This leads to overly optimistic, unrealistic performance estimates that do not translate to real-world applications. In compound activity prediction, a common form of leakage is compound overlap, where the same molecule appears in both the training and test sets due to inadequate splitting procedures [6].
Q2: Why is data leakage a critical issue for benchmarking single-cell foundation models (scFMs) and activity prediction models? For both scFMs and activity prediction models, data leakage creates a false impression of a model's capability to generalize to new, unseen data. This undermines the fairness of model comparisons and can misdirect research efforts. Preventing leakage is a foundational step in creating trustworthy benchmarks, as it ensures that performance metrics reflect true predictive power rather than the model's ability to "remember" training data [7] [8].
Q3: How can I identify potential data leakage in my experimental setup? Be vigilant for these warning signs:
- Unusually High Performance: If your model achieves near-perfect accuracy on a complex task with limited data, it may be memorizing data rather than learning generalizable patterns [6].
- Compound or Sample Overlap: Inspect your training and test splits to ensure no individual compound (for activity prediction) or cell (for scRNA-seq analysis) is present in both sets [6].
- Temporal or Procedural Confounding: Ensure that data from a later experiment (e.g., a confirmatory assay) is not used to train a model meant to predict results from an earlier screening stage [9].
Q4: What are the best practices for splitting data to prevent leakage in compound activity datasets? Standard random splitting is often insufficient. For rigorous benchmarking, use advanced cross-validation (AXV) or hold-out methods that operate at the compound level rather than the data point level [6]. This means that before generating data points (such as matched molecular pairs), a hold-out set of compounds is first removed. Any data point derived from a compound in this hold-out set is exclusively assigned to the test set, guaranteeing no compound overlap [6].
Case Studies & Experimental Protocols
Case Study 1: Large-Scale Prediction of Activity Cliffs
This study benchmarked machine and deep learning methods for predicting activity cliffs (ACs)—pairs of structurally similar compounds with large differences in potency. It highlighted how data leakage through compound overlap can significantly inflate perceived model performance [6].
Experimental Protocol:
- Data Extraction: 100 compound activity classes were extracted from ChEMBL (version 29), focusing on Ki or Kd measurements [6].
- AC Definition: Activity cliffs were defined using the Matched Molecular Pair (MMP) formalism. A critical step was using activity class-dependent potency difference criteria (mean potency plus two standard deviations) instead of a fixed threshold, making AC identification more statistically robust [6].
- Data Splitting (Leakage Prevention): The study implemented two splitting strategies to quantify the leakage effect:
- Data Leakage Possibly Included: Standard random 80/20 split of all MMPs.
- Data Leakage Excluded (AXV): A hold-out set of 20% of compounds was first created. MMPs were then assigned to training or test sets based on whether their constituent compounds were in the training or hold-out set [6].
- Molecular Representation: MMPs were represented using concatenated ECFP4 fingerprints for the core structure and the chemical transformation [6].
- Model Training & Evaluation: A range of models, from simple k-nearest neighbors to support vector machines and deep neural networks, were trained and evaluated on both data splits. Performance was measured using AUC (Area Under the Curve) [6].
Quantitative Results: The table below summarizes the performance impact of data leakage in this study [6].
| Model Complexity | Model Type | Average Performance (AUC, Leakage Included) | Average Performance (AUC, Leakage Excluded) | Performance Gap Due to Leakage |
|---|---|---|---|---|
| Low | k-Nearest Neighbors | 0.91 | 0.78 | 0.13 |
| Medium | Support Vector Machine | 0.93 | 0.80 | 0.13 |
| High | Deep Neural Network | 0.90 | 0.78 | 0.12 |
Case Study 2: The CARA Benchmark for Real-World Drug Discovery
The Compound Activity benchmark for Real-world Applications (CARA) was designed to address biases in existing benchmarks, including data leakage. It emphasizes the importance of distinguishing between different assay types—Virtual Screening (VS) and Lead Optimization (LO)—which have fundamentally different data distributions that can lead to inadvertent leakage if not handled properly [9].
- Experimental Protocol:
- Data Source & Assay Classification: Data was curated from the ChEMBL database. Assays were classified as VS (diverse compounds) or LO (congeneric compounds with high similarity) based on the pairwise similarity of their compounds [9].
- Task-Specific Splitting: Different data splitting schemes were designed for VS and LO tasks to reflect real-world application scenarios and prevent unrealistic information transfer [9].
- Evaluation under Low-Data Scenarios: The benchmark evaluates models in both few-shot and zero-shot scenarios, which are critical for assessing a model's generalizability without leakage [9].
- Key Finding: The study found that sophisticated training strategies like meta-learning were effective for VS tasks, but simpler QSAR models performed well for LO tasks, highlighting that benchmark design directly influences model selection and perceived performance [9].
The Scientist's Toolkit: Essential Research Reagents & Materials
The following table details key computational tools and data resources used in the featured case studies.
| Item Name | Function / Application | Relevance to Leakage Prevention |
|---|---|---|
| ChEMBL Database | A large-scale, open-source bioactivity database containing compound-property data from scientific literature [9] [6]. | Serves as the primary data source for building robust benchmarks. Requires careful preprocessing to avoid inherent biases. |
| Matched Molecular Pair (MMP) Formalism | A method to represent pairs of compounds that differ by a single chemical transformation [6]. | The fundamental data structure for AC prediction studies. Leakage prevention requires splitting at the compound level, not the MMP level. |
| Extended Connectivity Fingerprints (ECFP4) | A type of circular fingerprint that encodes molecular substructures and is widely used for chemical similarity searches and machine learning [6]. | A standard method for numerically representing molecules and MMPs for model input. |
| Advanced Cross-Validation (AXV) | A data splitting protocol that ensures no compounds in the training set are in the test set by using a compound-level hold-out [6]. | A core methodological tool for explicitly preventing data leakage in compound-centric prediction tasks. |
Experimental Workflow & Data Partitioning Diagrams
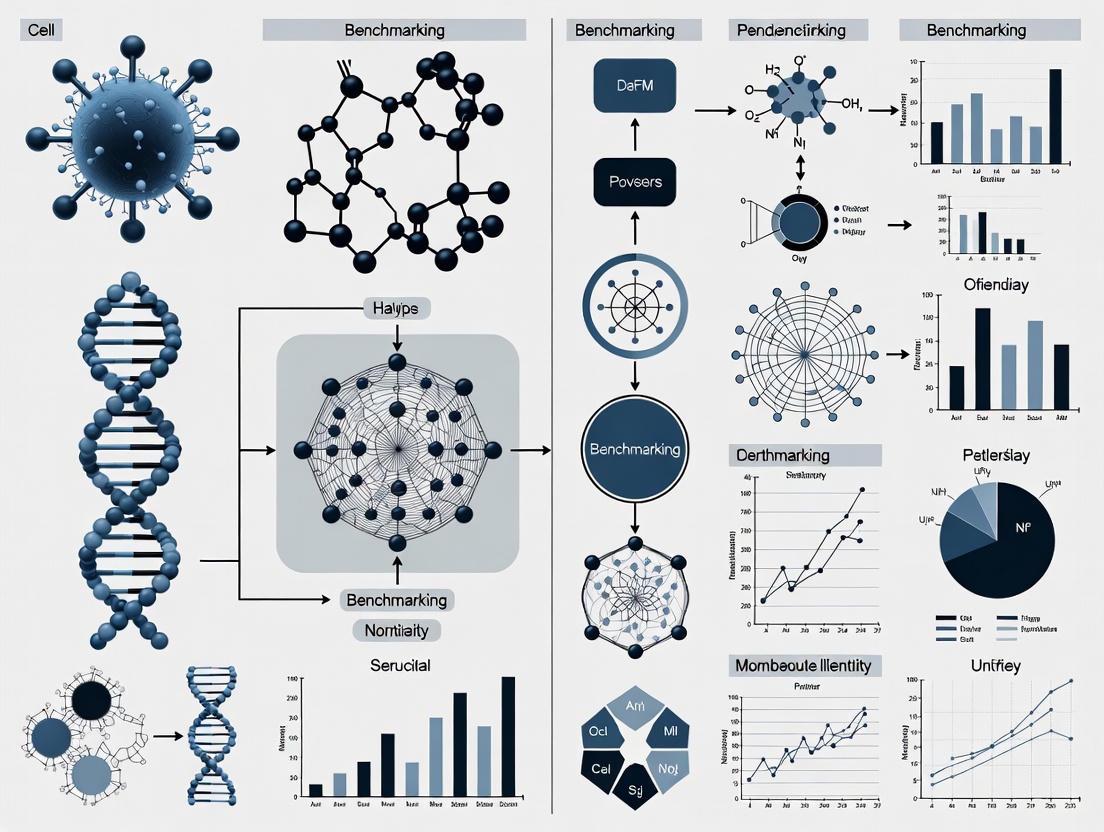
The following diagram illustrates the rigorous data partitioning strategy used to prevent data leakage in activity cliff prediction studies [6].
Data Splitting to Prevent Leakage
This workflow ensures no molecule in the test set is structurally related to any molecule in the training set, providing an unbiased evaluation.
The diagram below outlines the high-level process for creating a robust, leakage-free benchmark for computational models, integrating lessons from both case studies.
Leakage-Aware Benchmark Creation
FAQs on Data Leakage and Reproducibility
What is data leakage in the context of single-cell foundation model (scFM) benchmarking? Data leakage refers to the unintentional sharing of information between the training and evaluation phases of a model. In scFM benchmarking, this can severely compromise the validity of perturbation effect predictions. For instance, if information about a perturbation is indirectly learned during pre-training, the model's "zero-shot" prediction is no longer a true test of its understanding, but a reflection of this leaked information. The PertEval-scFM benchmark has highlighted that such issues can lead to models that fail to generalize, especially when faced with data that differs from their training set (a distribution shift) or when predicting strong/atypical perturbations [2].
Why is the distinction between reproducibility and replicability critical? These terms are often used interchangeably, but they refer to different validation stages. Reproducibility means using the original data and code to obtain the same results. Replicability means conducting a new, independent experiment and arriving at the same conclusions [10]. A study may be reproducible but not replicable if the original findings were a product of hidden data leakage or sampling error. True scientific rigor requires both.
How does data leakage contribute to the broader "replication crisis"? The replication crisis is the growing observation that many published scientific findings cannot be reproduced by other researchers [11]. Data leakage is a direct technical cause of this problem. It creates overly optimistic performance metrics during the initial study, leading to published results that cannot be replicated in real-world settings or independent labs. This wastes resources, as noted in reports that landmark findings in preclinical research have replication rates as low as 11-20% [11], and undermines trust in scientific literature [12].
What are common sources of data leakage in computational biology?
- Temporal Leakage: Using data from a "future" experiment to train a model meant to predict it.
- Preprocessing Leakage: Applying normalization or feature selection to the entire dataset before splitting it into training and test sets.
- Cross-Contamination in Splits: Inadequate splitting of single-cell data, where cells from the same donor or batch end up in both training and test sets, allowing the model to "memorize" donor-specific noise.
- Benchmarking Leakage: In scFM research, a model's pre-training data may inadvertently include information that is supposed to be held out for final evaluation on a benchmark task [2] [13].
Troubleshooting Guide: Preventing Data Leakage
| Problem | Symptom | Solution |
|---|---|---|
| Over-optimistic model performance | Model performs nearly perfectly on test data but fails on new, external data [2]. | Implement strict, domain-aware data splitting (e.g., by patient or batch). Use standardized frameworks like BioLLM for consistent evaluation [13]. |
| Failure to generalize | Model cannot predict effects under distribution shift or for strong perturbations [2]. | Apply rigorous cross-validation. Use holdout sets that are truly novel. Benchmark against simple baseline models to gauge true added value [2]. |
| Irreproducible results | Inability to obtain the same results from the original data and code [10]. | Practice open science: share all data, code, and analysis scripts. Use tools like the Open Science Framework for preregistration and sharing [10]. |
| High false positive rates | Findings are statistically significant in initial study but not in follow-up work [12]. | Preregister your study protocol and statistical analysis plan. Avoid p-hacking and HARKing (Hypothesizing After Results are Known) [14] [12]. |
Experimental Protocol: A Leakage-Free scFM Benchmarking Workflow
This protocol provides a methodology for conducting a robust, leakage-free benchmark of single-cell foundation models for perturbation effect prediction, based on frameworks like PertEval-scFM and BioLLM [2] [13].
1. Pre-Experimental Planning: Preregistration
- Action: Before any analysis, write and register a study protocol.
- Details: The protocol must specify the exact research question, the scFMs to be evaluated, the source and version of all benchmarking datasets, the primary outcome metric (e.g., accuracy in predicting perturbation effects), and the precise statistical tests to be used [14].
- Purpose: This prevents HARKing and outcome switching, safeguarding against conscious or unconscious bias.
2. Data Preparation and Curation
- Action: Establish a clean, held-out evaluation dataset.
- Details: For perturbation prediction, this involves compiling a dataset of post-perturbation gene expression profiles. Crucially, ensure that no information from these specific perturbation experiments was used in the pre-training data of any scFM being tested. Meticulous documentation of data provenance is key.
- Purpose: Creates a pure test set, free from pre-training contamination.
3. Model Integration and Zero-Shot Setup
- Action: Integrate scFMs using a unified framework and extract embeddings.
- Details: Use a framework like BioLLM, which provides standardized APIs for diverse scFMs (e.g., scGPT, Geneformer, scFoundation), eliminating architectural and coding inconsistencies [13]. In a zero-shot setup, the model's pre-trained embeddings are used directly without any further training on the benchmark task.
- Purpose: Ensures a fair and consistent comparison between different model architectures.
4. Evaluation and Baseline Comparison
- Action: Train a simple predictive model on the scFM embeddings and compare against baselines.
- Details: Train a simple classifier (e.g., logistic regression) on the extracted embeddings to predict perturbation effects. Compare its performance against simpler, non-contextualized baselines (e.g., models using raw gene expression counts). The PertEval-scFM benchmark found that scFM embeddings often do not provide consistent improvements over these baselines [2].
- Purpose: Determines whether the complex scFM provides tangible benefits over simpler, more interpretable methods.
5. Robustness and Sensitivity Analysis
- Action: Test model performance under varied conditions.
- Details: Evaluate the model on different subsets of data, such as strong vs. weak perturbations, or on data from a different laboratory or technology platform (distribution shift). Document where performance drops significantly.
- Purpose: Reveals the limitations and failure modes of the models, providing a more complete picture than a single aggregate performance score [2].
The following workflow diagram illustrates the key stages of this protocol, highlighting the critical points where data integrity must be enforced to prevent leakage.
The following table details essential computational tools and resources for conducting rigorous scFM benchmarking research.
| Item | Function in Research |
|---|---|
| BioLLM Framework | A unified system that simplifies the process of using, comparing, and improving diverse single-cell foundation models (scFMs) by providing standardized APIs and comprehensive documentation [13]. |
| PertEval-scFM Benchmark | A standardized framework designed specifically for the evaluation of models for perturbation effect prediction, enabling systematic comparison against simpler baseline models [2]. |
| Open Science Framework (OSF) | A infrastructure for supporting the research workflow, facilitating preregistration of study protocols, sharing of data and analysis code, and collaboration [10]. |
| Registered Reports | A publication format where peer review happens before data collection and results are known. This incentivizes high-quality research design and reduces publication bias for null results [14]. |
| Data Management Plan | A formal document that outlines what data will be collected, and how it will be organized, stored, handled, and protected during and after the research project to ensure long-term integrity and accessibility [14]. |
Quantitative Impact of the Reproducibility Crisis
The tables below summarize key quantitative findings that highlight the scale and impact of the reproducibility crisis across scientific fields.
Table 1: Replication Rates in Scientific Research
| Field | Replication Rate | Source / Context |
|---|---|---|
| Psychology | ~40% | AI-predicted likelihood of replicability for over 40,000 articles [10]. |
| Preclinical Cancer Research | <50% | Reproducibility Project: Cancer Biology found fewer than half of experiments were reproducible [12]. |
| Landmark Preclinical Studies | 11-20% | Reports from biotech companies Amgen and Bayer Healthcare [11]. |
Table 2: Perverse Incentives and Problematic Practices
| Issue | Statistic | Implication |
|---|---|---|
| Publication Bias for Positive Results | ~85% of published literature reports positive results [12]. | Creates a distorted, falsely successful scientific record. |
| Prevalence of HARKing | 43% of researchers admitted to doing it at least once [12]. | Increases the likelihood that false hypotheses are published. |
| Financial Cost in the U.S. | $28 Billion USD annually [12]. | Massive waste of research funding on non-reproducible work. |
Detailed Methodologies from Key Studies
1. PertEval-scFM: Benchmarking for Perturbation Effect Prediction
- Objective: To evaluate whether zero-shot embeddings from single-cell foundation models (scFMs) enhance prediction of transcriptional responses to perturbations compared to simpler baselines.
- Methodology:
- Framework Setup: A standardized evaluation framework (PertEval-scFM) was established to ensure consistent model comparison.
- Model Embedding Extraction: Multiple scFMs were used to generate contextualized embeddings for single-cell data in a zero-shot manner (no fine-tuning on the benchmark tasks).
- Baseline Model Training: Simpler, non-contextualized models (e.g., based on raw gene expression counts) were trained for the same perturbation prediction task.
- Performance Comparison: The predictive performance of classifiers trained on scFM embeddings was directly compared to the baseline models across various conditions, including distribution shifts and different perturbation strengths.
- Key Finding: The benchmark revealed that scFM embeddings did not provide consistent improvements over the simpler baseline models, and all models struggled with predicting strong or atypical perturbation effects [2].
2. AI-Powered Replicability Prediction
- Objective: To develop a procedure to accurately predict whether a given scientific study could be replicated without undertaking costly new experiments.
- Methodology:
- Model Training: A machine learning algorithm was trained to read the full text of scientific papers, analyzing cues in the writing (5,000-12,000 words) that correlate with replicability.
- Validation: The model was validated against known replication outcomes.
- Large-Scale Survey: The trained algorithm was applied to over 40,000 articles in top psychology journals published over 20 years to estimate the field's overall replicability rate.
- Key Finding: The model correctly predicted replication outcomes 65-78% of the time, and its survey suggested only about 40% of the studied psychology articles were likely to replicate [10].
Quick Reference: Types of Data Leakage
| Leakage Type | Brief Description | Common Example in scFM Benchmarking |
|---|---|---|
| Improper Data Splitting | Test data contaminates the training process, leading to over-optimistic performance. | Splitting cell data randomly by observation instead of by donor or batch, causing highly similar cells in both training and test sets [15]. |
| Feature Leakage | Using information for training that would not be available at the time of prediction in a real-world scenario. | In time-series prediction, using a future measurement (e.g., a later time point) to predict a past or present state [16] [15]. |
| Target Leakage | The training data includes a variable that is a direct proxy for the target itself. | A feature like "paymentstatus" is used to predict "loandefault"; the status is a direct consequence of the target [16]. |
| Preprocessing Leakage | Preprocessing steps (e.g., normalization, imputation) are applied to the entire dataset before splitting. | Calculating the mean and variance for normalization from the entire dataset (including test data) before splitting into train and test sets [16]. |
| Temporal Dependencies | Ignoring the time-dependent structure of data, violating the causal order of events. | In perturbation prediction, training on data collected after the time point you are trying to predict [16] [15]. |
Frequently Asked Questions
Q1: During scFM benchmarking, our model achieves near-perfect accuracy on the test set but fails completely on new experimental data. What could be the cause?
This is a classic sign of data leakage, most likely from Improper Data Splitting [15]. If your data splitting strategy does not account for the underlying biological structure, you will get optimistically biased performance. For example, in single-cell data, if cells from the same donor, culture, or sequencing batch are spread across both training and test sets, the model may learn to recognize technical artifacts or donor-specific signatures instead of the general biological signal of interest. When applied to a new dataset with different technical variations, the model's performance drops significantly [15].
Q2: What is the difference between a data leak and a data breach in the context of AI research?
This is a critical distinction. A data breach is a security incident where sensitive data is intentionally stolen by an unauthorized party, often through a cyberattack [16]. In contrast, data leakage in machine learning is a methodological error where information from outside the training dataset is unintentionally used to create the model [16] [15]. This leads to incorrect and irreproducible performance estimates, which is a primary focus in ensuring robust scFM benchmarking [17].
Q3: Our pipeline uses a standardized preprocessing step (like normalization) before splitting the data. Is this risky?
Yes, this practice, known as Preprocessing Leakage, is a common and serious risk [16] [18]. Any step that calculates statistics (like mean, standard deviation, or principal components) from the entire dataset before splitting will allow information from the test set to influence the training process. The model will be evaluated on data that it has already "seen" in a statistical sense, making it perform better than it would on truly independent, new data [16].
Q4: How can temporal dependencies cause leakage in predicting perturbation effects?
Temporal Dependencies are a major concern in dynamic biological processes. Leakage occurs when you use information from the future to predict the past [16] [15]. For instance, if you are building a model to predict a cell's state at time T, you must ensure that all data used for training was generated only up to time T. If your training data inadvertently includes measurements from time T+1, the model will learn this non-causal relationship and will fail to generalize to real-world scenarios where future data is, by definition, unavailable [16].
Troubleshooting Guide: Diagnosing and Fixing Leakage
Issue: Suspected Improper Splitting
- Symptoms: High performance on the held-out test set that does not replicate on a truly external validation set.
- Diagnosis: Check the splitting unit. Was the data split randomly by individual cells? If so, and your data has multiple cells per donor or batch, leakage is likely [15].
- Solution: Implement a group-based splitting strategy. Split the data by the independent experimental unit (e.g., by donor ID, cell culture plate, or sequencing batch). This ensures that all cells from one independent unit are entirely in either the training or the test set, providing a more realistic estimate of performance on new subjects [15].
Issue: Suspected Feature or Target Leakage
- Symptoms: The model's performance is unrealistically high, and upon inspection, you find a feature that seems to be a perfect predictor.
- Diagnosis: For every feature used in training, ask: "Would this information have been available in a real-world setting at the moment I need to make the prediction?" [16]
- Solution: Perform a thorough causal review of your features. Remove any variable that is set or collected after the event you are trying to predict or that is directly caused by the target variable [16].
Issue: Suspected Preprocessing Leakage
- Symptoms: The model performs well on the test set but fails when you try to preprocess new data and make predictions.
- Diagnosis: Review your code. Look for steps like normalization, imputation, or feature selection that are performed on the combined dataset.
- Solution: Structure your workflow as a pipeline. Treat all preprocessing steps as part of the model training. Learn the parameters (e.g., mean and variance for scaling) from the training set only, and then apply those learned parameters to the test set and any future data [18].
Experimental Protocol: A Leakage-Resistant scFM Benchmarking Workflow
The following diagram illustrates a robust workflow designed to prevent common data leakage sources in scFM benchmarking.
Step-by-Step Methodology:
- Initial Data Partitioning: This is the most critical step. Immediately after data collection and curation, split your dataset by the fundamental independent biological unit (e.g., donor ID, experimental batch, or cell culture). This prevents improper splitting by ensuring that correlated samples from the same source do not leak between training and test sets [15]. Keep the test set completely untouched and unseen until the final evaluation.
- Preprocessing and Featurization: Perform all data preprocessing steps (e.g., normalization, handling missing values, generating embeddings from an scFM) separately on the training set. Calculate all necessary statistics (mean, variance, etc.) and parameters from the training data only [18].
- Model Training: Train your machine learning model using only the preprocessed training data. Be vigilant for feature leakage; ensure no feature incorporates information that would be unavailable in a practical deployment scenario [16].
- Application to Test Set: Apply the preprocessing parameters and featurization models learned in Step 2 to the held-out test set. This simulates the arrival of new, unseen data.
- Final Evaluation: Evaluate the trained model's performance on the preprocessed test set. This performance metric provides a realistic estimate of how the model will generalize to new independent data, as all major leakage pathways have been controlled.
The Scientist's Toolkit: Essential Reagents for Robust Benchmarking
| Tool / Reagent | Function in Leakage Prevention |
|---|---|
| Group-Based Splitter | A software function that splits datasets by a grouping variable (e.g., patient ID), preventing improper splitting by ensuring all samples from a group are in the same partition (train or test) [15]. |
| Pipeline Automation Framework | A tool (e.g., from QSPRpred or scikit-learn) that encapsulates preprocessing and model training into a single object. This ensures test data is transformed using parameters learned from the training set alone, preventing preprocessing leakage [19] [18]. |
| Causal Feature Validator | A checklist or review process to vet each feature for target leakage. It forces the researcher to confirm: "Was this feature value known and fixed before the prediction target was determined?" [16] |
| Time-Aware Splitter | A data splitting function designed for temporal data. It ensures the training set only contains data from timepoints strictly before those in the test set, preventing leakage from temporal dependencies [16] [15]. |
| Standardized Benchmarking Framework (e.g., PertEval-scFM) | A standardized framework, like PertEval-scFM, provides a consistent and rigorous method to evaluate models, helping to reveal limitations and ensure that performance claims are not inflated by data leakage [2] [3]. |
Troubleshooting Guide: Data Leakage in scFM Benchmarking
This guide helps researchers identify and correct common data leakage scenarios that compromise single-cell foundation model (scFM) benchmarks and their application in drug discovery.
Q1: Our scFM performs perfectly in validation but fails to predict therapeutic targets in real patient samples. What went wrong? This classic sign of data leakage often stems from an incomplete separation of training and test data. In single-cell research, this can occur when cells from the same biological source or experimental batch are split across training and test sets. The model then learns to recognize technical artifacts rather than underlying biology [8]. To prevent this, ensure a strict, study-level split where all cells from an entire independent study or donor are assigned to either the training or test set, never both.
Q2: We incorporated a public dataset for fine-tuning. How can we be sure we haven't introduced leakage? Using public data requires vigilance. First, meticulously audit the metadata of the public dataset to ensure it does not contain any samples, donors, or cell lines that are also present in your test set, even if the sample identifiers are different [7]. Second, apply the same rigorous pre-processing and normalization pipeline to both your internal and external datasets to prevent the model from learning to distinguish sets based on technical, non-biological features [20].
Q3: Our model identifies strong biomarkers, but they are not biologically plausible. Could leakage be the cause? Yes. Highly significant but biologically nonsensical findings can be a red flag for a subtle form of temporal leakage. This happens when the model inadvertently accesses future or concurrent information that would not be available in a real predictive scenario [8]. Re-evaluate your feature selection process to ensure that only information available at the time of "prediction" is used during training. For perturbation prediction, this means the model should not be exposed to any post-perturbation data from the test set during its training phase [2].
Q4: What is the minimum number of perturbation examples needed to fine-tune an scFM without causing target leakage? Recent research indicates that even a modest number of experimental perturbations can significantly improve a model's predictive accuracy without inducing leakage, provided the data is handled correctly. Studies have shown that incorporating as few as 10-20 validated perturbation examples during fine-tuning can dramatically improve key metrics like sensitivity and specificity for predicting therapeutic targets [21]. The critical factor is that these perturbation examples must be distinct and properly excluded from the zero-shot evaluation of the model's general capabilities [21].
Quantitative Impact of Data Leakage on scFM Performance
The table below summarizes findings from benchmark studies that reveal how data leakage and distribution shifts can degrade model performance, leading to overly optimistic initial results.
Table 1: Performance Gaps in scFM Benchmarking Revealed by Rigorous Evaluation
| Evaluation Scenario | Metric | Reported Performance | Context & Caveats |
|---|---|---|---|
| Perturbation Effect Prediction (Zero-Shot) [2] [3] | General Performance | Limited improvement over simple baselines | Fails to provide consistent gains, especially under distribution shift. |
| Perturbation Effect Prediction (Zero-Shot) [2] [3] | Prediction of Strong/Atypical Effects | All models struggle | Highlights limitation in generalizability beyond training data distribution. |
| T-cell Activation (Open-loop ISP) [21] | Positive Predictive Value (PPV) | 3% | Very low PPV for open-loop in silico perturbation (ISP) predictions. |
| T-cell Activation (Open-loop ISP) [21] | Negative Predictive Value (NPV) | 98% | Open-loop ISP excels at identifying true negatives. |
| T-cell Activation (Closed-loop ISP) [21] | Positive Predictive Value (PPV) | 9% | 3-fold increase in PPV after fine-tuning with experimental perturbation data. |
Experimental Protocols for Leakage-Free scFM Benchmarking
Protocol 1: Implementing a Rigorous Train-Test Splitting Strategy for scFM Evaluation
- Objective: To create training and test sets that accurately reflect a model's ability to generalize to new, unseen biological conditions.
- Materials: Aggregated single-cell dataset (e.g., from CELLxGENE), computational environment.
- Methodology:
- Split by Study/Donor: Partition the data such that all cells from an entire independent study, patient donor, or experimental batch are assigned exclusively to the training or test set [7]. This prevents the model from learning study-specific technical biases.
- Hold-Out for Final Validation: Reserve one or more entire studies that are not used in any training or hyperparameter tuning phases. This serves as the final, unbiased test of generalizability [7].
- Stratification (if necessary): If the data partition leads to imbalanced cell type distributions between train and test sets, consider stratifying the splits at the study level to ensure all major cell types are represented in the test set.
- Expected Outcome: A significant drop in performance metrics (e.g., accuracy, F1-score) on the held-out test set compared to a leaky validation set, providing a realistic assessment of the model's utility.
Protocol 2: Closed-Loop Fine-Tuning for Enhanced Therapeutic Target Prediction
- Objective: To improve the predictive accuracy of a pre-trained scFM for a specific disease context (e.g., RUNX1-Familial Platelet Disorder) by incorporating a small number of experimental perturbations without causing data leakage [21].
- Materials: Pre-trained scFM (e.g., Geneformer), scRNA-seq data from disease model (e.g., RUNX1-knockout HSCs), scRNA-seq data from a limited set of genetic perturbations (e.g., Perturb-seq) in a relevant cell type.
- Methodology:
- Initial Fine-tuning: Fine-tune the scFM to distinguish the disease state (e.g., RUNX1-knockout) from the healthy control state using the available scRNA-seq data.
- Perturbation Incorporation: Further fine-tune this model using the labeled perturbation dataset. Critically, the labels should indicate the cellular state (e.g., "shifted-toward-healthy"), not the identity of the perturbed gene, to force the model to learn the phenotypic effect [21].
- In Silico Perturbation (ISP) Screening: Use the final fine-tuned model to perform in silico knockout or overexpression of genes across the genome. The model will predict which perturbations shift the disease state toward a healthy state.
- Validation: The top predicted therapeutic targets must be validated using orthogonal experimental methods (e.g., with specific small-molecule inhibitors) to confirm the model's predictions [21].
- Expected Outcome: A significant increase in the Positive Predictive Value (PPV) for identifying true therapeutic targets, as demonstrated by a three-fold improvement in a T-cell activation model [21].
Workflow Visualization
Diagram 1: A closed-loop framework for scFM fine-tuning incorporates experimental data to improve prediction accuracy for therapeutic target discovery [21].
Diagram 2: The cascade of consequences from data leakage in scFM pipelines, ultimately leading to costly R&D failures [7] [2] [21].
The Scientist's Toolkit: Key Research Reagents for scFM Benchmarking
Table 2: Essential Materials and Resources for Rigorous scFM Evaluation
| Resource / Reagent | Function in scFM Benchmarking |
|---|---|
| CELlxGENE Atlas [7] [20] | A primary source of standardized, annotated single-cell datasets used for large-scale model pretraining and for creating unbiased benchmark test sets. |
| Asian Immune Diversity Atlas (AIDA) v2 [7] | An independent, unbiased dataset used to mitigate the risk of data leakage and provide rigorous external validation of model generalizability. |
| Perturb-seq Data [21] | Single-cell RNA sequencing data from genetic perturbation screens (e.g., CRISPRi/a). Used for fine-tuning scFMs in a "closed-loop" framework to improve prediction accuracy. |
| Geneformer / scGPT [7] [20] [21] | Examples of prominent single-cell foundation models with different architectures and pretraining strategies, used as base models for fine-tuning and benchmarking. |
| PertEval-scFM Framework [2] [3] | A standardized benchmarking framework specifically designed to evaluate the performance of scFMs and other models for perturbation effect prediction. |
| scGraph-OntoRWR Metric [7] | A novel, knowledge-based evaluation metric that measures the consistency of cell type relationships captured by scFMs with prior biological knowledge from cell ontologies. |
Building Leakage-Proof scFM Benchmarks: A Step-by-Step Methodological Framework
Troubleshooting Guide: Common Data Preprocessing Pitfalls in Benchmark Creation
1. Issue: Data Leakage Between Training and Test Sets
- Problem: Model performance is optimistically biased because information from the test set inadvertently influences the training process.
- Solution: Implement a temporal split where the test set contains only cases that start after a defined separation time. For ongoing cases, events occurring before this time can be used to construct test prefixes, but their targets should be marked as "NAN" and excluded from inference [22].
- Advanced Check: Use data versioning tools like
lakeFSto create isolated branches for each preprocessing run, ensuring the exact data snapshot used for training is preserved and can be audited [23].
2. Issue: Inconsistent Dataset Documentation Leads to Irreproducible Results
- Problem: Preprocessing steps are inadequately documented, making it impossible to replicate the benchmark or compare results across studies.
- Solution: Adopt a principled, standardized preprocessing workflow and document all steps meticulously. Publicly share the scripts used to convert raw datasets into benchmarks [22].
3. Issue: Benchmark Suffers from Temporal and Representation Bias
- Problem: The test set is not representative of real-world scenarios, potentially favoring models that perform well only on specific case durations or types.
- Solution: Curate test sets to be unbiased concerning the mix of case durations and the number of running cases. Ensure the split is representative of the underlying process [22].
4. Issue: High Cardinality Categorical Variables and Complex Data Types
- Problem: Single-cell data or process mining events contain numerous categories or high-dimensional features, complicating the analysis.
- Solution: For categorical data, use encoding techniques like one-hot, label, or binary encoding. For high-dimensional data, employ dimensionality reduction techniques like Principal Component Analysis (PCA) [24]. Foundation models can be leveraged to extract meaningful features from such complex data [25].
Frequently Asked Questions (FAQs)
Q1: Why is principled data preprocessing so critical for creating public benchmarks in machine learning? Principled preprocessing is the foundation of reliable and unbiased research. It ensures that datasets are of high quality, models are trained and evaluated on correctly separated data, and results are reproducible. Inconsistent or flawed preprocessing leads to data leakage, biased performance metrics, and ultimately, a failure to compare different algorithms fairly, hindering scientific progress [22] [23].
Q2: What is the single most important rule to prevent data leakage in predictive process monitoring? The most critical rule is to enforce a strict temporal separation between training and test sets. The test set should only contain cases (or parts of cases) that started after all the data in the training set. This prevents the model from having access to future information during training, which is a common form of data leakage in temporal data [22].
Q3: How can I handle missing values in a benchmark dataset without introducing bias? Common techniques include:
- Removal: Deleting rows or columns with missing values, suitable for large datasets where removal doesn't cause significant data loss [23] [24].
- Imputation: Replacing missing values with a statistical measure like the mean, median, or mode of the available data [23] [24].
- Advanced Imputation: Using more sophisticated methods like k-nearest neighbors (KNN) imputation or multiple imputations by chained equations (MICE) for a more accurate estimate [24]. The choice depends on the data amount and the nature of the missingness.
Q4: What is the purpose of scaling and normalization in data preprocessing? Many machine learning algorithms are sensitive to the scale of input features. If features are on different scales, a feature with a larger range can disproportionately influence the model. Scaling and normalization transform all features to a comparable range, which helps models like Support Vector Machines and k-Nearest Neighbors converge faster and perform better [23] [24].
Q5: In the context of single-cell foundation model benchmarking, what are the key evaluation scenarios?
The scDrugMap framework, for instance, uses two primary evaluation strategies [25]:
- Pooled-Data Evaluation: Models are trained and tested on aggregated data from multiple studies. This tests the model's performance on a large, combined dataset.
- Cross-Data Evaluation: Models are trained on a collection of datasets and then tested independently on held-out datasets from individual studies. This tests the model's ability to generalize to new, unseen data sources.
Quantitative Data on Benchmark Datasets and Preprocessing
The following tables summarize quantitative data from benchmarking efforts and standard preprocessing techniques.
Table 1: Summary of Curated Single-Cell Data Collections for Drug Response Benchmarking [25]
| Data Collection | Number of Cells | Number of Datasets | Number of Studies | Key Characteristics |
|---|---|---|---|---|
| Primary Collection | 326,751 | 36 | 23 | Covers 14 cancer types, 3 therapy types, 5 tissue types, and 21 treatment regimens. |
| Validation Collection | 18,856 | 17 | 6 | Includes 5 cancer types and 3 therapy types; used for external testing. |
Table 2: Common Data Preprocessing Techniques and Their Applications [23] [24]
| Preprocessing Step | Common Techniques | Brief Description | Typical Use Case |
|---|---|---|---|
| Handling Missing Values | Listwise Deletion, Mean/Median Imputation, KNN Imputation | Removes incomplete rows/columns or infers missing values. | Preparing data for algorithms that cannot handle missingness. |
| Categorical Encoding | One-Hot Encoding, Label Encoding | Converts non-numerical categories into numerical format. | Making categorical data understandable for ML algorithms. |
| Feature Scaling | Min-Max Scaler, Standard Scaler, Robust Scaler | Brings all features to a similar scale. | Required for distance-based models (e.g., SVM, KNN). |
| Data Splitting | Temporal Split, Random Split | Divides data into training, validation, and test sets. | Evaluating model performance on unseen data; temporal splits prevent leakage. |
Table 3: Foundation Model Performance in Pooled-Data Evaluation (Primary Collection) [25]
| Foundation Model | Training Strategy | Mean F1 Score (Cell Line Data) | Key Takeaway |
|---|---|---|---|
| scFoundation | Layer Freezing | 0.971 | Top-performing model, significantly outperformed the lowest-performing model. |
| scBERT | Layer Freezing | 0.630 | Example of a lower-performing model in this specific evaluation scenario. |
Experimental Protocols for Benchmark Creation
Protocol 1: Creating Unbiased Benchmark Datasets from Event Logs (e.g., BPIC Challenges)
This protocol is based on principles to prevent data leakage and create representative test sets [22].
- Data Acquisition: Obtain the raw event log (e.g., in
.xesformat). - Define Separation Time: Choose a specific timestamp that splits the timeline. All cases that start after this point are eligible for the test set.
- Construct Training Set: Include all cases that were completed before the separation time.
- Construct Test Set:
- Identify cases that start after the separation time. These form the core of the test set.
- For ongoing cases that started before and ended after the separation time, events occurring before the separation time can be used to build prefixes. However, the target values for these prefixes must be set to "NAN" and excluded from model training and evaluation to prevent leakage.
- Add Prediction Targets: Augment the dataset with new columns for the specific prediction task:
- Remaining Time: Add a
remain_timecolumn. - Outcome: Add binary target columns (e.g.,
approved,declined,canceled). - Next Event: Add a
nextEventcolumn.
- Remaining Time: Add a
- Data Export: Save the training and test sets as separate files (e.g., CSV or Pickle for practicality with large datasets like BPIC_2017).
Protocol 2: Benchmarking Foundation Models for Single-Cell Drug Response Prediction
This protocol outlines the methodology for a comprehensive benchmarking study as implemented in scDrugMap [25].
- Data Curation and QC:
- Manually collect a large number of single-cell RNA-seq datasets from public studies.
- Perform quality control to filter out low-quality cells.
- Annotate cells with metadata: cancer type, tissue type, therapy type, and drug response status (sensitive/resistant).
- Split the curated data into a primary collection for main benchmarking and a separate validation collection for external testing.
- Model Selection: Choose a set of foundation models to evaluate, including both domain-specific models (e.g., scFoundation, scGPT, Geneformer) and general-purpose large language models (e.g., LLaMa).
- Model Adaptation:
- Strategy 1 (Layer Freezing): Keep the pre-trained weights of the foundation model frozen and train only a lightweight classification head on top.
- Strategy 2 (Fine-Tuning): Use Low-Rank Adaptation (LoRA) to efficiently fine-tune the foundation model on the specific drug response task.
- Evaluation:
- Pooled-Data Evaluation: Train and test models on the aggregated primary collection to assess overall performance.
- Cross-Data Evaluation: Train models on the primary collection and test them on the held-out validation collection to assess generalization to new data sources.
- Zero-Shot Evaluation: Test some models' pre-trained capabilities without any task-specific fine-tuning.
- Performance Analysis: Compare models based on metrics like F1 score across different data categories (tissue, cancer, drug class).
Experimental Workflow and Signaling Pathway Diagrams
Benchmark Creation Workflow
scFM Benchmarking Process
The Scientist's Toolkit: Research Reagent Solutions
Table 4: Essential Tools for Principled Data Preprocessing and Benchmarking
| Item | Function | Example / Note |
|---|---|---|
| Data Version Control (lakeFS) | Manages data lake versions with Git-like branching, ensuring reproducible preprocessing pipelines and isolating experiment runs [23]. | Critical for preventing non-deterministic pipelines and supporting ML governance. |
| Workflow Management (Apache Airflow) | Orchestrates complex data preprocessing workflows as Directed Acyclic Graphs (DAGs), automating the sequence of tasks [23]. | Ensures preprocessing steps are consistent and repeatable. |
| Single-Cell Foundation Models (scFoundation, scGPT) | Pre-trained models on large-scale scRNA-seq data that can be adapted via transfer learning for downstream tasks like drug response prediction [25]. | Provides a powerful starting point, often outperforming models trained from scratch. |
| Low-Rank Adaptation (LoRA) | A parameter-efficient fine-tuning technique that allows for effective adaptation of large foundation models without the cost of full fine-tuning [25]. | Reduces computational requirements and training time. |
| Python Data Libraries (pandas, scikit-learn) | Provide built-in functions and libraries for data manipulation, imputation, encoding, and scaling, streamlining the preprocessing code [23] [24]. | The standard toolkit for implementing preprocessing steps. |
| Benchmark Creation Scripts | Custom Python scripts (e.g., for converting BPIC datasets) that implement the principled preprocessing steps defined in research papers [22]. | Ensures the benchmark is created exactly as described, aiding reproducibility. |
FAQs: Understanding Data Partitioning
Q1: What is the primary goal of strategic data splitting in single-cell foundation model (scFM) benchmarking?
The primary goal is to prevent data leakage, which occurs when information from the test dataset inadvertently influences the model training process. This breach in the separation between training and test data leads to overly optimistic performance metrics that do not reflect the model's true ability to generalize to unseen data, thereby compromising the validity and reproducibility of the benchmarking study [26].
Q2: How does "assay-wise" partitioning differ from "compound-wise" partitioning?
- Assay-Wise Partitioning involves splitting the data based on experimental batches or technological platforms. This ensures that all data from a particular assay (e.g., a specific scRNA-seq protocol or a distinct drug sensitivity screen) is entirely contained within either the training or the test set. It tests the model's ability to generalize across different experimental conditions [27].
- Compound-Wise Partitioning involves splitting the data based on the entities being studied, such as different chemical compounds or distinct cell lines. This ensures that all data related to a specific compound is confined to a single split (training, validation, or test). It tests the model's ability to predict for entirely new compounds that were not seen during training [28].
Q3: What is a common, hidden source of data leakage in scFM workflows?
A common source is performing feature selection or data preprocessing on the entire dataset before splitting. When steps like Highly Variable Gene (HVG) selection or covariate regression are applied to the combined training and test data, information from the test set leaks into the training process. These operations must be performed independently on each split after the data has been partitioned [26] [29].
Q4: Why is a simple random split often insufficient for scFM benchmarking?
Simple random splitting does not account for the complex, nested structure of biological data. It can lead to non-representative splits where, for instance, highly similar biological replicates or technical replicates from the same donor end up in both training and test sets. This can artificially inflate performance, as the model is not being tested on a truly independent sample. Structured splits like assay-wise or compound-wise are necessary to rigorously assess generalizability [30] [27].
Troubleshooting Guides
Issue 1: Inflated Performance Metrics Despite Using a Separate Test Set
Problem Your scFM shows excellent performance on the test set during benchmarking, but this performance drastically drops when applied to new, external data. This is a classic symptom of data leakage.
Diagnosis and Solution Follow this diagnostic workflow to identify and remedy the source of leakage:
Issue 2: Implementing Compound-Wise Splitting for Drug Sensitivity Prediction
Challenge Creating a test set that contains entirely new compounds to realistically simulate a drug discovery scenario.
Step-by-Step Protocol
- Compound List Extraction: Compile a definitive list of all unique compounds (or cell lines) present in your entire dataset.
- Stratified Splitting: Use the
scikit-learnGroupShuffleSplitor a similar function. This ensures that the data is split based on the compound groups, and it can also attempt to preserve the overall distribution of a key variable (e.g., high vs. low sensitivity) in each split. - Validation of Splits: Manually verify that no compound appears in more than one data split (training, validation, and test). The following Python code demonstrates this process:
Issue 3: Managing Batch Effects with Assay-Wise Splitting
Challenge When splitting data by assay or batch, strong technical batch effects can make it difficult for the model to learn the underlying biology, causing poor performance.
Solution Strategy
- Acknowledge the Challenge: A drop in performance with a proper assay-wise split is a more honest reflection of the model's capability to handle batch variation.
- Consider Integration Tools: As part of the training process only, you can use batch integration methods (e.g., Harmony, Seurat, scVI) to align the training data from different assays [7]. It is critical that the integration model is learned only on the training data and then applied to the test data.
- Benchmark Robustly: Evaluate your scFM's "zero-shot" integration capabilities by comparing its performance on unintegrated test data against traditional integration methods applied in a leak-free manner [7].
Quantitative Impact of Data Leakage
The table below summarizes experimental data on how different types of data leakage inflate model performance, underscoring the importance of rigorous partitioning.
Table 1: Performance Inflation Caused by Data Leakage in Predictive Modeling (adapted from [26])
| Type of Data Leakage | Phenotype / Task | Baseline Performance (r) | Performance with Leakage (r) | Inflation (Δr) |
|---|---|---|---|---|
| Feature Leakage | Attention Problems Prediction | 0.01 | 0.48 | +0.47 |
| (Feature selection done on entire dataset) | Matrix Reasoning Prediction | 0.30 | 0.47 | +0.17 |
| Subject Leakage (20%) | Attention Problems Prediction | ~0.01 | 0.29 | +0.28 |
| (Data duplicates across splits) | Matrix Reasoning Prediction | ~0.30 | 0.44 | +0.14 |
| Family Leakage | Attention Problems Prediction | ~0.01 | 0.03 | +0.02 |
| (Related subjects in different splits) | Matrix Reasoning Prediction | ~0.30 | 0.30 | 0.00 |
The Scientist's Toolkit
Table 2: Essential Reagents and Computational Tools for Robust scFM Benchmarking
| Item / Tool Name | Type | Primary Function in Data Splitting & Leakage Prevention |
|---|---|---|
GroupShuffleSplit (scikit-learn) |
Computational Tool | Implements compound-wise or assay-wise splitting by ensuring data groups are not split across training and test sets. |
scGPT / Geneformer |
Single-Cell Foundation Model | Benchmarking targets; their zero-shot embeddings are tested on data partitioned with the strategies described here [7]. |
| Stratified Splitting | Computational Technique | Maintains the distribution of a key categorical variable (e.g., cell type, sensitivity class) across all data splits, preventing biased splits. |
| Harmony / scVI | Computational Tool | Batch integration methods used during training to correct for technical variation across assays, improving model learning on assay-wise split data [7]. |
| CellxGene Atlas | Data Resource | Provides high-quality, public single-cell datasets that can be used as an independent, unbiased test set to finally validate model performance and mitigate leakage risks [7]. |
| PAC-MAN | Computational Pipeline | A scalable analysis method for multi-sample cytometry data that handles batch effects and aligns clusters across samples, illustrating the importance of cross-sample partitioning [27]. |
Frequently Asked Questions (FAQs)
Q1: What is the primary goal of the CARA benchmark? The CARA (Compound Activity benchmark for Real-world Applications) benchmark is designed to provide a high-quality dataset and framework for developing and evaluating computational models that predict compound activity against target proteins. Its key goal is to offer a more realistic and practical evaluation by considering the biased distribution of real-world compound activity data, thereby preventing the overestimation of model performance that can occur with other benchmarks [9] [31].
Q2: How does CARA help prevent data leakage in benchmarking? CARA incorporates carefully designed train-test splitting schemes tailored to different drug discovery tasks, such as Virtual Screening (VS) and Lead Optimization (LO). This rigorous separation of training and test data helps prevent data leakage by ensuring that models are evaluated on assays and compound distributions that are not represented in the training set, mirroring real-world application scenarios and yielding more reliable performance estimates [9].
Q3: Why does CARA distinguish between Virtual Screening (VS) and Lead Optimization (LO) assays? This distinction is crucial because these two stages of drug discovery generate data with fundamentally different characteristics. VS assays typically contain compounds with a diffused distribution and lower pairwise similarities, representing diverse chemical libraries. In contrast, LO assays contain congeneric compounds with highly similar scaffolds, representing optimized chemical series. Models may perform differently on these tasks, so evaluating them separately provides more meaningful insights for real-world applications [9].
Q4: What are the consequences of data leakage in a benchmark? Data leakage, where information from the test set inadvertently influences the training process, leads to over-optimistic and biased performance estimates [8]. This makes a model appear more capable than it actually is, hinders fair comparison between different methods, and ultimately results in models that fail when deployed in real-world drug discovery settings [8] [32].
Q5: Which evaluation metrics are most relevant for real-world performance in CARA? CARA emphasizes evaluation metrics that align with practical utility. For VS tasks, this includes metrics that assess a model's ability to successfully rank active compounds. For LO tasks, the accurate prediction of activity cliffs (where small structural changes lead to large potency changes) is critical. The benchmark moves beyond simple binary classification to ensure recommendations are relevant for practice [9].
Troubleshooting Guides
Issue 1: Poor Model Generalization on New Assays
This issue occurs when a model performs well on its training data but fails to generalize to new, unseen assays, often due to biased data or incorrect data splitting.
- Problem: Model performance drops significantly on test assays.
- Solution: Adopt the CARA data splitting protocol.
- Procedure:
- Assay Classification: First, classify your assays as either VS-type (diffused compound distribution) or LO-type (congeneric compounds) [9].
- Stratified Splitting: Ensure that during train-test splitting, all data from a single assay (representing a specific experimental condition and target) is entirely contained within either the training set or the test set. This prevents information leakage from assay-specific biases [9].
- Task-Specific Evaluation: Evaluate your model's performance on VS and LO assays separately to identify its specific strengths and weaknesses [9].
Issue 2: Managing Few-Shot and Zero-Shot Learning Scenarios
In real-world discovery, you may have very few or no measured activities for a new target. Standard models often fail in these low-data regimes.
- Problem: Your model is unable to make accurate predictions when only a few (few-shot) or no (zero-shot) task-related data points are available.
- Solution: Implement meta-learning or multi-task learning strategies.
- Procedure:
- Strategy Selection: Based on CARA's findings, for VS tasks, leverage training strategies like meta-learning or multi-task learning across many different assays to build a more generalizable model [9].
- Model Design: For few-shot prediction of continuous compound activities, consider architectures specifically designed for this purpose, which aggregate encodings from known compounds to capture assay information [33].
- Validation: Rigorously validate the model in a hold-out setting that simulates the few-shot or zero-shot scenario before applying it to a truly new target.
Issue 3: Detecting and Mitigating Data Contamination
Data contamination happens when test data, or data very similar to it, is present in the training set, invalidating the benchmark results.
- Problem: You suspect your benchmark results are unrealistically high due to data contamination.
- Solution: Proactively construct contamination-free benchmarks.
- Procedure:
- Automated Screening: Use automated frameworks like AntiLeakBench to screen for and exclude data points that contain knowledge likely present in the training sets of modern AI models [32].
- Knowledge Recency: Construct benchmark samples using explicitly new knowledge (e.g., from recent scientific literature published after the model's training cutoff date) to ensure a strictly contamination-free evaluation [32].
- Audit Training Data: Maintain meticulous records of your training data sources and versions to trace the origin of potential contamination.
Experimental Protocols & Data
Core Experimental Workflow of the CARA Benchmark
The following diagram illustrates the key steps in constructing and applying the CARA benchmark to ensure a realistic and leakage-free evaluation.
Quantitative Data from the CARA Benchmark
The table below summarizes key characteristics of the two main assay types defined in the CARA benchmark, which necessitate different modeling approaches [9].
Table 1: Characteristics of VS and LO Assays in the CARA Benchmark
| Assay Type | Discovery Stage | Compound Distribution | Pairwise Similarity | Typical Modeling Goal |
|---|---|---|---|---|
| Virtual Screening (VS) | Hit Identification | Diffused, Widespread | Low | Identify active compounds from large, diverse libraries. |
| Lead Optimization (LO) | Hit-to-Lead / Lead Optimization | Aggregated, Concentrated | High (Congeneric) | Accurately rank and predict activities of similar compounds. |
Essential Reagents for Computational Experimentation
This table lists key resources and their functions for researchers looking to work with or build upon benchmarks like CARA.
Table 2: Key Research Reagent Solutions for Benchmarking
| Item Name | Function / Application |
|---|---|
| ChEMBL Database | A primary, publicly available source of bioactive, drug-like molecules providing curated compound activity data for training and evaluation [9]. |
| CARA Benchmark Dataset | Provides a pre-processed, high-quality dataset with assay classifications and splitting schemes designed for real-world drug discovery applications [9] [31]. |
| Meta-Learning Algorithms | Training strategies (e.g., MAML, Prototypical Networks) used to improve model performance in few-shot learning scenarios for VS tasks [9]. |
| AntiLeakBench Framework | An automated tool for constructing and updating benchmarks with new knowledge to prevent data contamination and ensure fair model evaluation [32]. |
Data Leakage Prevention Framework
A robust benchmarking workflow must incorporate specific steps to prevent data leakage, as shown in the following protocol.
Data leakage occurs when information from outside the training dataset—particularly from the target variable or validation/test sets—is unintentionally used during the feature engineering process [34]. This problem creates overly optimistic performance metrics during model development but leads to significant performance degradation when models are deployed in real-world scenarios where the leaked information is unavailable [34] [35].
In the context of single-cell foundation model (scFM) benchmarking research, data leakage poses a particularly critical challenge. When evaluating scFMs for tasks like perturbation effect prediction, leakage can invalidate benchmark results and lead to incorrect conclusions about model capabilities [3] [2]. Understanding and preventing data leakage is therefore essential for producing reliable, reproducible research that accurately reflects model performance.
FAQs: Understanding Data Leakage
What are the most common types of data leakage in feature engineering?
The most prevalent types of data leakage in feature engineering include:
Target Leakage: Occurs when features include information that directly reveals the target variable [36] [35]. For example, in a model predicting loan repayment, including a feature like "repayment_status" would leak the answer [36].
Temporal Leakage: Happens with time-series data when future information is used to predict past events [34] [36]. For instance, using stock prices from next week to predict today's price.
Train-Test Contamination: Occurs when information from the test set leaks into the training process, often through improper preprocessing [36] [35]. This can happen when scaling or normalization is applied before data splitting.
Feature Leakage: When features indirectly contain information too closely related to the target variable [36]. For example, using "total sales in last 30 days" to predict whether a product will sell next period.
Why is data leakage particularly problematic for scFM benchmarking?
Data leakage severely compromises scFM benchmarking for several reasons:
Overestimated Capabilities: Leakage can make scFMs appear more capable than they truly are, particularly in zero-shot settings where they're expected to generalize without fine-tuning [3] [2].
Invalid Comparisons: When leakage affects some models but not others, benchmark comparisons become invalid and misleading [37].
Irreproducible Results: Findings affected by leakage cannot be reproduced in real-world applications, wasting research resources and impeding scientific progress [35].
How can I detect potential data leakage in my feature set?
Several techniques can help identify potential data leakage:
Correlation Analysis: Analyze correlations between each feature and the target variable [34]. Features with unusually strong correlations may indicate leakage.
Segment Analysis: Divide samples based on feature values and inspect target ratios within each segment [34]. This can reveal partial data leaks that affect only a subset of samples.
Temporal Validation: For time-series data, validate that no future information is available at prediction time [34].
Domain Expertise: Collaborate with domain experts to validate that features don't inadvertently leak target information [36] [35].
Troubleshooting Guides
Problem: Model performs well during training but fails in production
Diagnosis: This classic pattern suggests data leakage during feature engineering or training [34] [35]. The model learned patterns from information that won't be available in production environments.
Solution:
- Audit Feature Engineering Pipeline: Ensure all feature engineering operations are computed using only training data statistics [34] [35].
- Implement Time-Aware Validation: For temporal data, use time-based cross-validation to ensure the model isn't seeing future information [34].
- Check Feature Dependencies: Verify that no features incorporate information that would be unavailable at prediction time [36].
Problem: Unexpected performance drop after hyperparameter tuning
Diagnosis: Hyperparameter tuning might have accidentally incorporated information from the validation set, causing overfitting to specific evaluation metrics.
Solution:
- Use Nested Cross-Validation: Implement nested cross-validation where hyperparameter tuning occurs in an inner loop separated from the outer evaluation loop.
- Isolate Tuning Data: Keep a completely separate dataset for final model evaluation after hyperparameter tuning.
- Monitor for Overfitting: Track performance differences between training and validation sets during tuning iterations.
Problem: Features show unusually high correlation with target variable
Diagnosis: Some features may be directly or indirectly leaking information about the target variable [34] [36].
Solution:
- Conduct Feature Lineage Analysis: Trace how each feature is created and identify any dependencies on the target variable.
- Analyze Timing Dependencies: Ensure all feature values would be available at the time of prediction in a real deployment scenario.
- Consult Domain Experts: Verify the causal relationship between features and target makes logical sense [36].
Experimental Protocols for Leakage-Free Benchmarking
Protocol 1: Proper Data Splitting for scFM Evaluation
Purpose: To ensure clean separation between training, validation, and test sets without leakage.
Materials: Single-cell dataset (e.g., from CellxGene [37]), computational environment.
Methodology:
- Initial Splitting: Split data into training (70%), validation (15%), and test (15%) sets before any preprocessing [35].
- Stratified Splitting: Maintain similar distributions of key biological variables (cell types, conditions) across splits.
- Temporal Considerations: For time-series single-cell data, use chronological splitting where training data precedes validation and test data [34].
- Identity Tracking: Ensure the same cell doesn't appear in multiple splits.
Protocol 2: Cross-Validation for scFM Benchmarking
Purpose: To reliably estimate model performance without data leakage.
Materials: Training dataset, evaluation metrics.
Methodology:
- Fold Creation: Split training data into k folds (typically k=5 or k=10).
- Iterative Training: For each fold:
- Use k-1 folds for training
- Use the remaining fold for validation
- Compute all feature engineering statistics (means, variances) from the k-1 training folds only
- Performance Aggregation: Calculate average performance across all folds.
- Final Evaluation: Apply the final model to the completely held-out test set.
Table 1: scFM Benchmarking Results Without Data Leakage
| Model | Batch Integration Score (ASW) | Cell Type Annotation (Accuracy) | Perturbation Prediction (MSE) | Data Leakage Check |
|---|---|---|---|---|
| scGPT | 0.72 | 0.89 | 0.14 | Pass |
| Geneformer | 0.68 | 0.85 | 0.18 | Pass |
| scVI (baseline) | 0.65 | 0.82 | 0.16 | Pass |
| UCE | 0.71 | 0.87 | 0.15 | Pass |
Protocol 3: Temporal Validation for Longitudinal Single-Cell Studies
Purpose: To prevent temporal leakage when working with time-series single-cell data.
Materials: Time-stamped single-cell data, computational environment.
Methodology:
- Time Point Definition: Identify all distinct time points in your dataset.
- Chronological Splitting: Assign earlier time points to training and later time points to testing.
- Rolling Window Validation: For time-series cross-validation:
- Train on initial time window
- Validate on subsequent time window
- Roll the windows forward
- Feature Engineering Constraint: Ensure all features for a given time point use only information from previous time points.
Essential Research Reagent Solutions
Table 2: Key Computational Tools for Leakage-Free Feature Engineering
| Tool/Resource | Function | Application in scFM Research |
|---|---|---|
| dotData Feature Factory | Automated feature engineering with leakage prevention [34] | Automatically manages temporal lead time in single-cell feature discovery |
| PertEval-scFM Benchmark | Standardized framework for evaluating perturbation prediction [3] [2] | Provides leakage-free evaluation protocol for scFMs |
| Time-based Cross-Validation | Prevents temporal leakage in longitudinal studies [34] | Essential for evaluating scFMs on time-course single-cell data |
| scGraph-OntoRWR Metric | Cell ontology-informed evaluation metric [37] | Measures biological consistency of scFM embeddings without leakage |
| Seurat & Harmony | Baseline methods for single-cell data analysis [37] | Provide reference points for scFM benchmarking |
Workflow Visualization
Data Processing Without Leakage
scFM Benchmarking Protocol
Implementing Robust Cross-Validation Schemes Tailored for scFM Data
Troubleshooting Guides & FAQs
Frequently Asked Questions
Q1: Why is my scFM model performing perfectly on benchmark data but failing on our new, internal dataset?
This is a classic sign of data leakage. It likely means your model was evaluated on data it was indirectly exposed to during its pre-training phase, inflating its perceived performance on the benchmark. When faced with truly novel data, its generalization capabilities are poor [38]. To diagnose this, investigate the pre-training corpus of the scFM you are using to check for overlaps with your benchmark data.
Q2: What are the most common but subtle forms of data leakage in scFM benchmarking?
The most prevalent and impactful form is feature selection leakage, where feature selection (e.g., identifying Highly Variable Genes) is performed on the entire dataset before splitting into training and test sets. This allows information from the test set to influence the training process [26]. Another form is subject-level leakage, which occurs when data from the same donor, batch, or family structure are spread across both training and test sets, violating the assumption of data independence [26].
Q3: How does the size of my dataset influence the risk of data leakage?
Smaller datasets are significantly more susceptible to the inflationary effects of data leakage. The performance inflation caused by leakage is more dramatic in models with weaker baseline performance, which are often trained on smaller datasets. As dataset size increases, the relative impact of leakage on performance metrics tends to decrease [26].
Q4: Beyond performance inflation, what other aspects of a model are affected by data leakage?
Data leakage can severely distort the biological interpretability of your model. When leakage occurs, the features (genes or pathways) identified as most important by the model may be misleading and not reflect true biological signals, leading to incorrect scientific conclusions [7].
Troubleshooting Common Experimental Issues
Problem: Suspected Feature Leakage in Pre-Processing
- Symptoms: Abnormally high prediction accuracy on a task that typically has low signal-to-noise ratio (e.g., predicting subtle clinical outcomes).
- Solution: Implement nested cross-validation. The inner loop is used for all pre-processing steps, including feature selection and hyperparameter tuning. The outer loop is used solely for evaluating the final model's performance. This strictly separates the test data from any aspect of model training [26].
Problem: Inflated Performance Due to Non-Independent Data
- Symptoms: The model generalizes well to data from the same study or batch but fails on external validation data.
- Solution: Perform structured data splitting. When creating your training and test sets, partition the data at the level of donors, experimental batches, or families—not at the individual cell level. This ensures that all cells from a single independent biological unit are entirely contained within either the training or the test set [26].
Problem: Uncertainty in Model Selection for a New scFM Task
- Symptoms: Not knowing which of the many available scFMs (e.g., Geneformer, scGPT, scFoundation) is best suited for a specific task.
- Solution: Consult holistic benchmarking studies and use the Roughness Index (ROGI) as a guide. Recent research provides task-specific model rankings. Furthermore, ROGI can act as a dataset-dependent proxy for model performance; a lower landscape roughness in the latent space often correlates with better task-specific learning [7].
Quantitative Data on Data Leakage Effects
The tables below summarize empirical data on how different types of leakage inflate model performance, underscoring the critical need for robust validation.
Table 1: Performance Inflation from Feature Leakage in Connectome-Based Models (Illustrative Example)
| Phenotype | Baseline Performance (r) | Performance with Feature Leakage (r) | Inflation (Δr) |
|---|---|---|---|
| Attention Problems | 0.01 | 0.48 | +0.47 |
| Matrix Reasoning | 0.30 | 0.47 | +0.17 |
| Age | 0.80 | 0.83 | +0.03 |
Data adapted from a study on connectome-based machine learning, demonstrating that leakage most severely inflates performance on tasks with a low initial signal [26].
Table 2: Impact of Subject-Level Leakage (20% Data Duplication)
| Phenotype | Baseline Performance (r) | Performance with 20% Subject Leakage (r) | Inflation (Δr) |
|---|---|---|---|
| Attention Problems | 0.01 | 0.29 | +0.28 |
| Matrix Reasoning | 0.30 | 0.44 | +0.14 |
| Age | 0.80 | 0.84 | +0.04 |
Duplicating subjects in a dataset, a form of subject-level leakage, leads to significant performance inflation, particularly for weaker models [26].
Table 3: Data Leakage in Software Engineering LLM Benchmarks (Illustrative Example)
| Benchmark Name | Leakage Ratio | Impact on Performance (Pass@1) |
|---|---|---|
| QuixBugs | 100.0% | Not Specified |
| BigCloneBench | 55.7% | Not Specified |
| APPS | 10.8% | 4.9x higher on leaked samples |
Data from a large-scale analysis of 83 software engineering benchmarks, showing that leakage can be pervasive in some benchmarks and drastically inflates key performance metrics [38].
Experimental Protocols for Leakage Prevention
Protocol 1: Nested Cross-Validation for scFM Fine-Tuning
Purpose: To provide an unbiased estimate of model performance when hyperparameter tuning and feature selection are required.
- Split Dataset: Split the entire dataset into K outer folds (e.g., K=5).
- Iterate Outer Folds: For each outer fold
i:- Set fold
iaside as the external test set. - Use the remaining K-1 folds for an inner cross-validation loop:
- Split the K-1 folds into L inner folds.
- Use these inner folds to perform feature selection and hyperparameter tuning. All pre-processing must be fit only on the inner training folds and then applied to the inner validation fold.
- Train a final model on the entire K-1 folds using the best parameters and features identified in the inner loop.
- Evaluate this model on the outer test set (fold
i), which has played no role in pre-processing or parameter tuning.
- Set fold
- Aggregate Results: The final performance is the average of the K performance scores from the outer test sets [26].
Protocol 2: Structured Data Splitting for Single-Cell Data
Purpose: To prevent leakage from non-independent cellular data.
- Identify Independent Units: Determine the level of biological and technical independence in your data. This could be individual donors, experimental batches, or family structures.
- Group by Unit: Group all cells by their respective independent unit.
- Stratified Splitting: Perform the train/test or cross-validation split on the level of these independent units, not individual cells. This ensures all cells from one donor, for example, are entirely in the training set or entirely in the test set.
- Verify Splits: Check that no independent unit is represented in both the training and test sets [26].
Protocol 3: DetectLeak Framework for Benchmark Contamination Checks
Purpose: To systematically identify if your evaluation benchmark data was present in an LLM's (or scFM's) pre-training corpus.
- Data Preparation: Obtain the scFM's pre-training dataset (
D_construct) and your evaluation benchmark dataset (D_eval). - Near-Duplicate Detection: Use an efficient algorithm like MinHash with Locality-Sensitive Hashing (LSH) to scan for potential duplicate pairs between the two datasets. This efficiently handles the comparison of billions of data pairs [38].
- Manual Verification: Have domain experts (e.g., biologists, bioinformaticians) manually label the potential duplicates flagged by the automated tool to confirm true duplicates and rule out false positives.
- Quantification & Curation: Calculate the leakage ratio (number of leaked samples / total benchmark samples). To ensure future evaluations are fair, create a cleaned benchmark with the identified leaked samples removed [38].
Experimental Workflow Visualization
Diagram 1: Robust scFM Cross-Validation Workflow.
Table 4: Key Resources for Robust scFM Benchmarking
| Item | Function & Description |
|---|---|
| Nested Cross-Validation Script | A computational script (e.g., in Python/R) that automates the nested CV process, ensuring no leakage between inner tuning and outer evaluation loops. |
| Structured Data Splitter | A tool that partitions single-cell data based on metadata (e.g., donor_id, batch) to preserve data independence between training and test sets. |
| MinHash + LSH Framework | An efficient algorithm for detecting near-duplicate samples between a pre-training corpus and an evaluation benchmark to identify data leakage [38]. |
| Roughness Index (ROGI) | A metric that quantifies the smoothness of the cell-property landscape in a model's latent space, serving as a proxy for potential task-specific performance [7]. |
| Cell Ontology-Informed Metrics (e.g., LCAD) | Evaluation metrics like Lowest Common Ancestor Distance (LCAD) that use biological knowledge to assess the severity of cell type annotation errors, improving biological interpretability [7]. |
| LessLeak-Bench / Cleaned Benchmarks | A version of a popular benchmark that has been curated to remove samples identified as leaked, enabling more reliable model evaluation [38]. |
Troubleshooting scFM Benchmarks: Identifying and Correcting Data Leakage Pitfalls
► FAQ: Troubleshooting Data Leakage
What is data leakage in the context of machine learning and scFM benchmarking? In machine learning, particularly in single-cell foundation model (scFM) benchmarking, data leakage refers to a flaw where information from outside the training dataset is inadvertently used to create the model. This includes information that would not be available at the time of a real-world prediction. It leads to over-optimistic, unrealistically high performance during training and testing that does not generalize to production or real biological applications [16].
What are the most common types of data leakage I should look for? The most prevalent types of data leakage that can invalidate your benchmark results include [16]:
- Target Leakage: When your training data includes a feature or variable that is a direct proxy for the target you are trying to predict. For instance, using a "payment status" field to predict loan default.
- Train-Test Contamination: This occurs when the strict separation between training and test datasets is violated. A common example is applying preprocessing steps (like normalization or imputation) to the entire dataset before splitting it into train and test sets.
- Feature Leakage: This involves engineered features that rely on future or otherwise unavailable information. For example, creating a feature based on the average customer spending over the past year, but calculating that average using data from after the prediction point.
Our model performed excellently on the benchmark but failed in a real-world perturbation prediction. Could data leakage be the cause? Yes, this is a classic symptom of data leakage. A model suffering from data leakage will demonstrate performance that seems too good to be true on held-out test data but will fail to generalize to new, real-world data. This is the direct consequence of the model learning the patterns of the specific test setup rather than the underlying biological problem. Recent benchmarking of scFMs for zero-shot perturbation effect prediction has shown that their embeddings do not consistently improve predictions, and all models struggle with strong or atypical perturbations, highlighting the critical need for leakage-free evaluation [2].
How can I prevent preprocessing leakage? The most effective protocol is to treat your preprocessing steps as part of the model itself. You must fit any preprocessing parameters (like the mean and standard deviation for normalization) only on the training data. Then, you use those parameters to transform both the validation and test datasets. This ensures no information from the test set leaks back into the training process [16].
What is the difference between implementation efficacy and effectiveness, and why does it matter for benchmarking? This distinction is crucial for interpreting benchmark results [39]:
- Implementation Efficacy: Measures performance under ideal, highly supported conditions (e.g., with extensive researcher oversight, dedicated computational resources). This answers "Can it work under the best circumstances?"
- Implementation Effectiveness: Measures performance under typical, resource-constrained real-world settings. This answers "Does it work in routine practice?" A benchmark that demonstrates efficacy does not guarantee effectiveness. Over-optimism arises when efficacy findings are assumed to predict real-world performance without accounting for the complexities and constraints of actual research environments [39].
► Diagnostic Protocol: Identifying Data Leakage
A systematic approach is required to diagnose the root causes of data leakage and over-optimistic performance. The following workflow and diagnostics table provide a structured method for investigation.
Diagram 1: A diagnostic workflow for identifying common types of data leakage.
Key Performance Indicators for Leakage Detection
The following table summarizes quantitative red flags and their diagnostic interpretations. A significant manifestation of any of these indicators suggests a high probability of data leakage in your experimental pipeline.
| Quantitative Red Flag | Diagnostic Interpretation | Example Scenario in scFM Benchmarking |
|---|---|---|
| Performance drop when moving from benchmark test set to a truly external validation set or real-world data [2] [39]. | Indicates the model learned dataset-specific patterns instead of general biological principles. The benchmark likely suffered from train-test contamination or feature leakage. | An scFM achieves high accuracy on a published perturbation benchmark but fails to predict effects in data from a new, independent laboratory. |
| Near-perfect performance on a complex prediction task (e.g., AUC >0.99) [16]. | Suggests the model may have access to a feature that is a direct proxy for the target variable (target leakage). | A model predicting a specific cellular response shows unrealistically high accuracy because a feature inadvertently encodes the response outcome. |
| Large discrepancy between cross-validation scores and hold-out validation scores. | A classic sign of train-test contamination, often because preprocessing was applied before data splitting. | Normalizing gene expression data across all samples before splitting into training and test sets, leaking global distribution information. |
| Model performance that is significantly better than established, simpler baseline models [2]. | While improved performance is the goal, a vast and unexpected superiority warrants investigation for leakage, as the complex model may be better at exploiting leaked information. | A sophisticated deep learning scFM fails to outperform a simple linear model when both are evaluated without leakage on a zero-shot perturbation task. |
► The Scientist's Toolkit: Key Research Reagents & Solutions
This table details essential methodological components and tools for constructing a robust, leakage-free benchmarking pipeline for single-cell foundation models.
| Item / Solution | Function & Role in Leakage Prevention |
|---|---|
| Stratified Data Splitter | A software function that handles the partitioning of data into training, validation, and test sets while preserving the distribution of key variables (e.g., cell type, donor). Its primary function is to prevent initial contamination between data splits. |
| Preprocessing Pipeline Encapsulation | A software design pattern that ensures all data preprocessing steps (normalization, scaling, imputation) are "fitted" exclusively on the training set and then applied to validation/test sets. This is the primary defense against preprocessing leakage [16]. |
| PRECIS-2 Framework (Adapted) | A conceptual tool from implementation science used to score how much a study reflects real-world conditions (effectiveness) versus idealized lab conditions (efficacy). Using this framework helps temper optimism about real-world performance by making study design choices explicit [39]. |
| Feature Auditor | A process or tool for systematically reviewing each feature in the dataset to check for chronological or logical dependencies that could introduce target leakage. It answers: "Would this information be available in a real-world scenario at the moment of prediction?" |
| PertEval-scFM Benchmark | A standardized framework specifically designed for the evaluation of single-cell foundation models on perturbation effect prediction. It provides a structured and consistent environment for leakage-free zero-shot evaluation [2]. |
FAQs on Data Partitioning and Leakage Prevention
This section addresses common challenges researchers face when partitioning data for single-cell foundation model (scFM) benchmarking, providing targeted solutions to prevent data leakage.
FAQ 1: What constitutes improper partitioning, and why is it a critical issue in scFM benchmarking? Improper partitioning occurs when data from the same biological source or batch is spread across training, validation, and test sets. This introduces data leakage, causing models to learn dataset-specific technical artifacts (like batch effects) rather than generalizable biological principles. For scFMs, this leads to overly optimistic performance metrics during benchmarking and models that fail to generalize to new, unseen datasets or biological conditions [20].
FAQ 2: What are the most common sources of data leakage in single-cell genomics workflows? The most common sources are:
- Batch Effects Across Splits: When cells from the same sequencing batch or experiment are present in multiple splits, the model may learn to identify the batch rather than the cell type [20].
- Individual-Based Leakage: Splitting data randomly at the cell level, instead of by individual donor or sample, allows information from the same donor to leak into all splits. The model then learns donor-specific signatures [20].
- Incorrect Gene Ordering during Tokenization: Some scFMs use gene expression rankings for tokenization. If the entire dataset is used to determine this order before splitting, information leaks into the training process [20].
- Improper Normalization: Applying dataset-wide normalization techniques before partitioning the data can allow information from the test set to influence the training set.
FAQ 3: How does "Individual-Based Splitting" prevent data leakage? Individual-Based Splitting partitions data at the level of the biological donor or sample, not individual cells. This ensures that all cells from a single donor are confined to only one of the splits (training, validation, or test). This method rigorously evaluates a model's ability to generalize its predictions to entirely new individuals, which is crucial for robust biological discovery and reliable drug development applications [20].
FAQ 4: Our dataset has a large class imbalance in a rare cell type. How can we partition the data without losing these cells in the test set? Use Stratified Individual-Based Splitting. First, group cells by individual donor. Then, partition the donors in a way that preserves the approximate percentage of the rare cell type across the training, validation, and test sets. This ensures the rare population is represented in the test set for a fair evaluation. The
scikit-learntrain_test_splitfunction with thestratifyparameter can be used for this purpose [40].FAQ 5: What key metrics indicate that data leakage may have occurred in our benchmark? The following metrics, especially in combination, are strong indicators of potential data leakage:
- Performance on the test set is nearly identical to, or even surpasses, performance on the training set.
- A significant and unexpected drop in performance when the model is evaluated on a truly external dataset from a different source.
- The model achieves near-perfect accuracy on tasks known to have high biological noise or technical variation.
The tables below provide a structured comparison of partitioning strategies and key metrics for diagnosing data leakage.
- Table 1: Comparison of Data Partitioning Strategies for scFM Benchmarking
| Partitioning Method | Splitting Unit | Data Leakage Risk | Generalizability Assessment | Recommended Use Case |
|---|---|---|---|---|
| Individual-Based | Donor/Sample | Very Low | High (to new individuals) | Primary method for robust scFM benchmarking [20]. |
| Batch-Based | Experimental Batch | Low | High (to new batches) | When batch effects are the primary concern [20]. |
| Random Cell-Based | Single Cell | Very High | Low | Not recommended for final benchmarking; can be used for initial model exploration [40]. |
| Stratified Individual-Based | Donor (by cell type) | Low | High (preserves rare populations) | Imbalanced datasets with rare cell types [40]. |
- Table 2: Key Metrics for Diagnosing Data Leakage in scFM Experiments
| Metric | Typical Leakage Signature | Investigation Action |
|---|---|---|
| Train-Test Accuracy Gap | Test accuracy >> Training accuracy | Audit the partitioning procedure for donor or batch overlap [40]. |
| Cross-Dataset Performance | High internal test performance but large drop on external data | Validate on a completely held-out dataset from a different lab or protocol [20]. |
| Per-Cell Prediction Confidence | High confidence on incorrect, biologically implausible classifications | Check for technical confounders (e.g., sequencing depth) that are correlated with the label. |
| Batch Effect Association | Model predictions are highly correlated with batch identity | Perform a differential analysis of model embeddings between batches. |
Experimental Protocol: Implementing Individual-Based Splitting
This protocol provides a step-by-step methodology for correctly implementing individual-based splitting to prevent data leakage in your scFM benchmarks.
Objective: To partition a single-cell RNA sequencing dataset into training, validation, and test sets such that all cells from any single biological donor appear in only one set, thereby preventing data leakage and enabling a valid assessment of model generalizability.
Materials:
Procedure:
- Data Preprocessing: Begin with a quality-controlled cell-by-gene count matrix. Perform initial filtering based on quality control metrics.
- Identify Unique Donors: Extract the
donor_idmetadata for all cells. Compile a list of all unique donor identifiers. Critical Step: All subsequent splitting is performed on this list of donors, not on individual cells. - Stratification (Optional but Recommended): If dealing with a rare cell type, calculate the proportion of that cell type for each donor. This proportion will be the stratification variable.
- Perform the Splits:
- First Split: Use
train_test_split()fromscikit-learnto separate the list of unique donors into a temporary training set (e.g., 70% of donors) and a combined validation-test set (e.g., 30% of donors). Use thestratifyparameter if performing stratified splitting [40]. - Second Split: Apply
train_test_split()again to the combined validation-test set to split it into a final validation set (e.g., 15% of original donors) and a final test set (e.g., 15% of original donors).
- First Split: Use
- Map Splits Back to Cells: Filter the original cell-level dataset to create the final training, validation, and test sets by including only those cells whose
donor_idis in the corresponding list of donors for that split. - Post-Split Normalization: Crucial Step. Perform any normalization (e.g., log-normalization, scaling) separately within each split. Calculate normalization parameters (e.g., mean, variance) from the training set only, and then use these parameters to transform the validation and test sets.
Validation of the Split:
- Verify that no
donor_idis present in more than one split. - Check that the distribution of key cell types is similar across splits, confirming successful stratification if applied.
- Verify that no
The Scientist's Toolkit: Research Reagent Solutions
Essential computational tools and data resources for implementing robust data partitioning in scFM research.
| Item | Function in Experiment |
|---|---|
scikit-learn (train_test_split) |
A Python library function used to randomly split the list of unique donors into training, validation, and test sets, ensuring no data leakage at the individual level [40]. |
| CZ CELLxGENE Platform | A curated, open-data resource providing access to millions of single-cell datasets with standardized metadata, which is essential for accurately mapping cells to their donor of origin [20]. |
| Pandas DataFrame | The primary data structure in Python used for handling metadata, managing the list of donors, and mapping split results back to the full cell-level dataset. |
| Scanpy / Seurat | Standard toolkits for single-cell data analysis. They are used for quality control, filtering, and within-split normalization after the partitioning is complete. |
| Hash Partitioning (PySpark) | In distributed computing environments, this method ensures that all data from a single donor (key) is directed to the same computational partition, maintaining integrity for large-scale analysis [41]. |
Workflow and Pathway Diagrams
The following diagrams illustrate the core workflow for proper data partitioning and the logical relationship between different splitting strategies.
Individual-Based Splitting Workflow
Data Partitioning Strategy Decision Tree
Mitigating Bias from Congeneric Compounds and Biased Protein Exposure
FAQs and Troubleshooting Guide
This technical support resource addresses common challenges in data leakage prevention for single-cell fusion mass cytometry (scFM) benchmarking research. The guidance is framed within the principles of data integrity to ensure reliable and reproducible results [42].
Q1: How can I determine if congeneric compounds are introducing analytical bias in my scFM data?
- A: Congeneric compounds can cause bias by interfering with antibody binding or metal tags, leading to signal suppression or enhancement. To troubleshoot, first run a control experiment using a cell line known to be negative for the target protein. Spiked-in congeneric compounds at relevant concentrations should not produce a positive signal in this negative control. A significant signal shift suggests analytical bias. Furthermore, review your metal-tagged antibody panels for potential isotopic overlaps or chemical similarities with the congeneric compounds, as these can be a source of interference [42].
Q2: What are the best practices to prevent data leakage when benchmarking scFM computational tools?
- A: Data leakage, where information from the test set influences the training process, severely biases performance estimates. To prevent this [42]:
- Implement Rigorous Data Governance: Apply ALCOA++ principles to ensure data is Attributable, Legible, Contemporaneous, Original, and Accurate, as well as Complete, Consistent, Enduring, Available, and Traceable. This includes maintaining a secure, version-controlled audit trail for all data splits [42].
- Separate Data Splits Early: Partition your data into training, validation, and test sets at the very beginning of your analysis, prior to any preprocessing or feature selection.
- Preprocess Independently: Fit preprocessing parameters (e.g., scaling, normalization) solely on the training set, and then apply these parameters to the validation and test sets.
- Use Holdout Sets: For final evaluation, use a completely held-out test set that is only used once, after the model is fully tuned.
- A: Data leakage, where information from the test set influences the training process, severely biases performance estimates. To prevent this [42]:
Q3: My experiment shows high background signal. Could this be from biased protein exposure or reagent issues?
- A: High background can stem from both biological and technical sources. To diagnose [42]:
- Technical Check: Titrate your antibodies to determine the optimal concentration that minimizes non-specific binding. Include a fluorescence-minus-one (FMO) control to set appropriate gating boundaries and identify background from spectral overlap.
- Biological Assessment: If technical issues are ruled out, biased protein exposure due to cellular stress, apoptosis, or fixation/permeabilization artifacts could be the cause. Validate your findings using a different analytical technique, such as Western blotting, on a subset of samples to confirm the protein expression levels.
- A: High background can stem from both biological and technical sources. To diagnose [42]:
Q4: What methodologies can mitigate bias from congeneric compounds during sample preparation?
- A: Implement robust sample preparation protocols [42]:
- Sample Cleanup: Use solid-phase extraction (SPE) or protein precipitation to remove congeneric compounds prior to labeling and analysis.
- Buffer Optimization: Incorporate detergents or blocking agents in your staining buffer to reduce non-specific binding caused by interfering compounds.
- Validation with Standards: Use stable isotope-labeled internal standards for the congeneric compounds. Consistent recovery rates of these standards across samples indicate that bias from matrix effects is being controlled.
- A: Implement robust sample preparation protocols [42]:
Experimental Protocols for Bias Mitigation
The following table summarizes key quantitative data and methodologies for core experiments in this field.
| Experiment Objective | Key Measured Variables | Positive Control | Acceptance Criteria | Primary Risk Mitigation |
|---|---|---|---|---|
| Assessing Congeneric Compound Interference | Signal shift in negative control cells; CV > 20% indicates issue [42] | Cells with known high target expression | Signal in negative control < 2x background [42] | Sample cleanup (SPE); use of internal standards [42] |
| Validating scFM Panel Specificity | Median Signal Intensity (MSI) of target vs. isotype control; Staining Index | Titrated antibody on positive cell line | Staining Index > 3 for clear separation [42] | Comprehensive antibody titration; FMO controls [42] |
| Data Leakage Prevention in Benchmarking | Model performance metrics (e.g., AUC, F1-score) on holdout test set | A simple baseline model (e.g., random forest) | AUC on test set within 2% of validation AUC [42] | ALCOA++ data governance; early data partitioning [42] |
Detailed Protocol 1: Assessing Congeneric Compound Interference
- Sample Preparation: Prepare three sets of samples: (1) negative control cells, (2) negative control cells spiked with the congeneric compound at the highest expected concentration, and (3) a positive control cell line.
- Staining and Acquisition: Process all samples identically through your standard scFM staining protocol and acquire data on the mass cytometer.
- Data Analysis: Compare the median signal intensity of the channel of interest for sample sets (1) and (2). A statistically significant increase (e.g., p-value < 0.05 using a t-test) in set (2) indicates interference.
- Quality Control: The positive control (set 3) must show a strong positive signal to confirm the assay is working correctly. The coefficient of variation (CV) for technical replicates should be below 20% [42].
Detailed Protocol 2: Implementing a Data Leakage Prevention Workflow
- Data Governance Policy: Establish a standard operating procedure (SOP) based on ALCOA++ principles. This defines how data is handled, accessed, and versioned, ensuring an audit trail records all changes without obscuring original entries [42].
- Pre-Analysis Partitioning: Before any analysis, randomly split your annotated single-cell data into three sets: Training (70%), Validation (15%), and Test (15%). Securely archive the Test set.
- Model Training & Tuning: Use the Training set to fit models. Use the Validation set to tune hyperparameters. All feature selection must be based only on the Training set.
- Final Evaluation: Apply the final, tuned model to the held-out Test set only once to obtain an unbiased estimate of its real-world performance. Document all steps in the audit trail [42].
Signaling Pathways and Experimental Workflows
Experimental Bias and Data Integrity Workflow
Data Leakage Prevention Protocol
Research Reagent Solutions
The following table details essential materials and their functions for mitigating bias in scFM experiments.
| Reagent / Material | Primary Function | Key Consideration for Bias Mitigation |
|---|---|---|
| Metal-Tagged Antibodies | Label target proteins for detection by mass cytometry. | Titrate to optimal concentration to minimize non-specific binding and signal spillover [42]. |
| Cell Viability Dye | Identify and exclude dead cells from analysis. | Prevents biased protein exposure data from compromised cell membranes [42]. |
| Isotype Controls | Measure non-specific antibody binding (background). | Critical for setting accurate positive gates and identifying reagent-based bias [42]. |
| FMO Controls | Determine background fluorescence and spreading error for each channel. | Essential for accurate gating in high-parameter panels to prevent misclassification bias [42]. |
| Stable Isotope-Labeled Internal Standards | Account for variability in sample preparation and instrument response. | Corrects for signal suppression/enhancement from congeneric compounds or matrix effects [42]. |
| Solid-Phase Extraction (SPE) Kits | Clean up samples by removing congeneric compounds and salts. | Reduces analytical interference that can cause inaccurate quantification [42]. |
| Calibration Beads | Normalize signal intensity across different acquisition runs. | Ensures data consistency and comparability, a core principle of data integrity (Consistent) [42]. |
| Validated Cell Lines | Serve as positive and negative controls for assay validation. | Provides a ground truth to confirm that the assay is detecting real biological signals accurately [42]. |
Frequently Asked Questions (FAQs)
Q1: What is the primary goal of Virtual Screening (VS) versus Lead Optimization (LO)? Virtual Screening aims to rapidly identify initial "hit" compounds with activity against a biological target from extremely large virtual or physical libraries. Its key attributes are speed and the ability to capture most potential actives, rather than high prediction accuracy for every compound [43]. In contrast, Lead Optimization is a pivotal, multidisciplinary process that transforms a "hit" compound into a "lead" with enhanced potency, selectivity, and pharmacokinetic properties suitable for further development [44].
Q2: When should I transition from VS to LO assays? The transition typically occurs when you have identified one or more confirmed hits from high-throughput or virtual screening that show reproducible activity. The H2L process then begins to optimize these hits across multiple parameters, including potency in primary and secondary assays, selectivity, and early ADME (Absorption, Distribution, Metabolism, Excretion) profiling [44].
Q3: How can data leakage impact the benchmarking of computational models in drug discovery? Data leakage, where information from the test set inadvertently influences the training process, makes research results hard or even impossible to reproduce and compare [8]. In predictive process monitoring, this often manifests as training and test sets not being completely separated. This poses a significant challenge to the field's progress by compromising the fair competition of ideas and the validity of model performance claims [8].
Q4: What are the best practices for creating unbiased benchmark datasets? Creating unbiased benchmarks requires principled preprocessing steps to ensure representative test sets without data leakage [8]. This involves rigorous quality control standards for input data and standardized evaluation protocols that prevent non-standardized data splits or the use of non-public domain knowledge, which can hamper fair competition and reproducibility [7] [8].
Q5: What key properties should be optimized during Lead Optimization? The LO phase involves iterative "design-make-test-analyze" cycles to optimize a wide range of properties [44]. The table below details the typical parameters for Hit-to-Lead optimization.
| Parameter Category | Specific Properties |
|---|---|
| Potency | Primary screening assay, secondary in vitro assay(s) [44] |
| Selectivity | Off-target activity, orthologues relevant in the screening cascade [44] |
| Physicochemical Profile | Solubility, lipophilicity [44] |
| ADME Profile | Protein binding, membrane permeability, plasma stability, liver microsomal stability [44] |
| Safety | Cellular toxicity (in vitro) [44] |
| In Vivo Profile | Pharmacokinetics [44] |
Q6: How do simpler machine learning models compare to complex foundation models for specific tasks? According to benchmark studies, simpler machine learning models can be more adept at efficiently adapting to specific datasets, particularly under resource constraints [7]. Notably, no single complex foundation model consistently outperforms others across all tasks, emphasizing the need for tailored model selection based on factors such as dataset size, task complexity, and computational resources [7].
Troubleshooting Guides
Issue: High False Positive Rate in Virtual Screening
Problem: Virtual screening results in an unmanageably large number of hits, many of which turn out to be inactive or non-viable in confirmatory assays.
Solution:
- Apply Property Filtering: Implement the "Rule of Five" (RO5) criteria early in the screening process. Poor absorption or permeation is more likely when a compound has:
- Molecular Weight (MW) > 500
- Calculated logP (CLOGP) > 5
- Hydrogen Bond Donors (HDO) > 5
- Hydrogen Bond Acceptors (HAC) > 10 [43]
- Filter Reactive Compounds: Exclude molecules that are reactive toward protein targets (e.g., Michael acceptors, ketones, aldehydes, suicide inhibitors), as these often yield false positives in HTS [43].
- Use Consensus Scoring: Rely on target-trained or consensus scoring schemes when evaluating docking results to improve the reliability of hit identification [43].
Issue: Poor Pharmacokinetic Properties in Lead Compounds
Problem: Lead compounds show good binding affinity in vitro but have poor ADME properties (e.g., low solubility, high metabolic clearance) that hinder their in vivo efficacy.
Solution:
- Shift Optimization Strategy: It is often easier to optimize pharmacokinetic properties early in drug discovery and improve receptor binding affinity at a later stage [43].
- Integrate ADME Assays Early: Incorporate ADME profiling into the initial lead optimization cycles. Key assays should include:
- Solubility: To ensure adequate dissolution.
- Lipophilicity: A key driver of permeability and metabolic stability.
- Microsomal Stability: To predict metabolic clearance.
- Plasma Protein Binding: To understand free drug concentration [44].
- Adopt a Parsimonious Approach: Select candidate leads that already have reasonably good ADME properties for further optimization, rather than starting with compounds that have major liabilities [43].
Issue: Data Leakage in Single-Cell Foundation Model (scFM) Benchmarking
Problem: Benchmarking results for scFMs are not reproducible or are overly optimistic due to data leakage between training and test sets.
Solution:
- Implement Rigorous Splits: Ensure training and test sets are completely separated. For single-cell data, this requires special attention to prevent leakage particular to predictive process monitoring [8].
- Use Unbiased Benchmarks: Employ benchmark datasets created with data leakage prevention in mind. These datasets should be biologically representative and have splits that reflect real-world application scenarios, such as novel cell types or cross-tissue homogeneity [7].
- Standardize Evaluation: Utilize unified frameworks like BioLLM, which provide standardized APIs and preprocessing pipelines to ensure consistent and fair model evaluation, thereby mitigating the risk of data leakage from inconsistent processing steps [45].
Experimental Protocols & Workflows
Protocol 1: Standardized Workflow for Benchmarking Foundation Models
This protocol, based on established benchmarking frameworks, is designed to evaluate computational models fairly and prevent data leakage [7] [8] [45].
- Data Acquisition and Curation: Collect high-quality datasets with accurate labels. For biological models, this includes datasets spanning diverse conditions, such as different tissues, patients, or experimental technologies [7].
- Data Preprocessing: Apply a rigorous, standardized quality control pipeline to all datasets. This step must be consistent across all models being evaluated [45].
- Data Partitioning: Split the data into training, validation, and test sets in a principled way that prevents information leakage. This may involve ensuring that similar biological conditions or processes are not spread across different sets [8].
- Model Initialization & Training: Load models (in zero-shot or fine-tuned mode) using a unified framework to ensure consistent implementation and hyperparameter handling [45].
- Task Execution & Evaluation: Run the models on the held-out test set and evaluate performance using multiple, pre-defined metrics. For scFMs, this can include:
- Embedding Quality: Using metrics like Average Silhouette Width (ASW).
- Biological Fidelity: Using ontology-informed metrics like scGraph-OntoRWR.
- Prediction Accuracy: Standard classification metrics for tasks like cell-type annotation [7].
The following diagram illustrates this workflow and the critical checkpoints for preventing data leakage.
Protocol 2: Integrated Hit-to-Lead Optimization Cascade
This protocol outlines the multidisciplinary "design-make-test-analyze" cycle for transforming a hit into a lead candidate [44].
- Compound Design (Design): Medicinal chemists design new compound derivatives based on emerging structure-activity relationship (SAR) data. Continuous patent database queries are conducted to support a solid Intellectual Property (IP) position.
- Compound Synthesis (Make): The designed compounds are synthesized.
- Primary and Secondary Profiling (Test): Newly generated compounds are run through a predefined screening cascade (a series of assays) to collect data on key parameters. The specific assays are determined by a detailed target compound profile.
- Data Analysis and Decision Making (Analyze): Accumulated data from the cascade is analyzed to guide the next cycle of compound design. Compounds are evaluated against the target profile to determine if they are suitable to progress to the next stage.
The iterative nature of this workflow is shown below.
The Scientist's Toolkit: Key Research Reagents & Materials
The following table lists essential components and their functions in a typical Hit-to-Lead optimization campaign [44].
| Research Reagent / Material | Function in H2L Optimization |
|---|---|
| Primary Target Assay | Confirms the initial activity and potency of hit compounds against the intended biological target. |
| Secondary In Vitro Assays | Provides more detailed pharmacological characterization (e.g., mechanism of action, functional activity). |
| Selectivity Panels (Off-Targets) | Evaluates compound specificity against unrelated targets to minimize potential side effects. |
| Solubility/Lipophilicity Assays | Measures key physicochemical properties critical for oral bioavailability and drug-like behavior. |
| ADME Profiling Assays | Assesses Absorption, Distribution, Metabolism, and Excretion parameters (e.g., protein binding, metabolic stability). |
| Cellular Toxicity Assay | Provides an early in vitro safety profile to identify potentially toxic compounds. |
| Structured Data Management System | Critical for handling and managing chemical compounds and the large volumes of data generated in iterative cycles. |
FAQs on Data Classification and Leakage Prevention
Q1: What is the fundamental difference between rule-based and AI-powered automated data classification?
Rule-based classification relies on predefined patterns (like regex for credit card numbers) to identify sensitive data. While useful for structured data, it often misses nuanced, unstructured information because it lacks context [46]. AI-powered automated classification uses machine learning and natural language processing to understand the context and content of data. It can distinguish between, for example, a resume and a medical record without manual rule creation, offering greater accuracy and coverage at scale [46] [47].
Q2: Why is accurate data classification critical for effective Data Leakage Prevention (DLP) in a research environment?
Accurate data classification provides the foundational labels that DLP systems use to enforce security policies [46]. If data is misclassified—for instance, if sensitive research data is labeled as "Public"—DLP systems will not block its unauthorized transmission. Proper classification ensures that security controls are applied to the correct assets, reducing false positives and preventing missed threats [48] [46]. This is essential for protecting intellectual property and complying with regulations like HIPAA in drug development.
Q3: What are common reasons an automated leak check or DLP system might fail to prevent data loss?
Common failure points include:
- Mislabeled Data: The DLP engine acts on classification labels; if labels are incorrect, protection fails [46].
- Insufficient Context Awareness: Traditional systems may not understand when a legitimate business process requires transferring sensitive data, leading to bypasses [46].
- Complex Data Environments: The growth of unstructured data in cloud apps, emails, and collaboration tools like Teams creates visibility gaps that are hard to cover without advanced discovery and classification [46].
- Evolution of Threats: As cyber threats become more sophisticated, static DLP rules require continuous updates to remain effective [49].
Q4: How can our team integrate data classification into existing data workflows without disrupting research?
The most effective strategy is to integrate classification directly into the tools where data is created and used. This includes:
- Using APIs and Micro-Integrations: Embedding classification into data creation points ensures data is tagged at the source [47].
- Leveraging Existing Platforms: Utilizing tools that integrate with platforms like Microsoft Purview to apply smart labels automatically based on AI-driven analysis [46].
- Adopting No-Code Tools: Implementing user-friendly, no-code solutions that allow researchers to apply classification within their spreadsheets and documents without IT assistance [48].
Table 1: Key Features of Modern Data Classification Tools
| Feature | Description | Benefit to Researchers |
|---|---|---|
| AI-Powered Context Understanding | Uses NLP and ML to understand data meaning, not just patterns [46]. | Accurately identifies sensitive research data without manual rules. |
| Real-Time Operation | Classifies data as it is created or modified within workflows [48]. | Provides immediate protection with minimal disruption. |
| Integration with Business Tools | Works within existing platforms (e.g., Google Sheets, Microsoft 365) [48]. | Eliminates the need for context-switching and simplifies adoption. |
| Custom Rule Creation | Allows creation of business-specific classification logic [48]. | Tailors data protection to specific research projects and data types. |
| Automated Discovery & Inventory | Scans and catalogs data across cloud, email, and databases [46]. | Provides a complete view of all sensitive data assets for risk assessment. |
Table 2: Data Leakage Prevention (DLP) Market Data and Projections
| Segment | Details | Projected CAGR (2025-2033) | Key Drivers |
|---|---|---|---|
| Overall DLP Solutions Market | Estimated market size of USD 6,800 million by 2025 [49]. | ~12% [49] | Escalating data breaches, stringent global regulations (GDPR, CCPA) [49]. |
| Cloud-Based DLP Solutions | A key segment within the DLP market [49]. | (Not specified, but high growth) | Shift to cloud services and need to protect data in transit and at rest [49] [50]. |
| Automatic Leak Test Apparatus Market | Global market valued at approx. $2.5 billion in 2023 [51]. | ~6% (2023-2028) [51] | Stringent quality control in pharma, food processing, and chemicals [51]. |
Experimental Protocols for Data Security Benchmarking
Protocol 1: Establishing a Baseline for Data Classification Accuracy
This protocol measures the effectiveness of a classification system before and after integrating AI.
- Objective: To quantify the accuracy and coverage of a data classification system in identifying sensitive research data.
- Materials:
- A curated test dataset containing 1,000 files and database entries. This set should include a mix of:
- Known sensitive data (e.g., patient records, chemical compound formulas).
- Public data (e.g., published papers, press releases).
- Ambiguous data that requires context for classification.
- The data classification tool or system under test (e.g., Numerous.ai, Concentric AI, Microsoft Purview).
- A pre-defined classification taxonomy (e.g., Public, Internal, Confidential, Restricted).
- A curated test dataset containing 1,000 files and database entries. This set should include a mix of:
- Methodology: a. Manually tag the entire test dataset to establish a ground truth. b. Run the classification tool against the test dataset. c. Compare the tool's output against the ground truth. d. Calculate key metrics: * Precision: (True Positives) / (True Positives + False Positives) * Recall: (True Positives) / (True Positives + False Negatives) * F1-Score: The harmonic mean of precision and recall.
- Analysis: A system with high recall but low precision generates many false alarms. A system with high precision but low recall misses too much sensitive data. The F1-score provides a single metric for balanced comparison. AI-driven systems are expected to show significantly higher F1-scores than rule-based ones [46].
Protocol 2: Simulating and Detecting a Data Leakage Event
This protocol tests the entire pipeline from data classification to leakage prevention.
- Objective: To verify that a DLP system correctly blocks or flags attempted exfiltration of classified data.
- Materials:
- A configured DLP solution (e.g., Symantec DLP, Microsoft DLP) integrated with the data classification system from Protocol 1.
- A test endpoint (laptop or virtual machine) with the DLP agent installed.
- A file containing data classified as "Restricted."
- Methodology: a. From the test endpoint, attempt to transfer the "Restricted" file through several channels commonly monitored by DLP: * Channel 1: Email as an attachment to a personal email account. * Channel 2: Upload to an unapproved cloud storage service (e.g., personal Dropbox). * Channel 3: Copy to a removable USB drive. b. For each channel, document the DLP system's response: does it block the transfer, quarantine the file, send a real-time alert, or log the event? [48] [49] c. Repeat the test with a "Public" file to ensure legitimate transfers are not blocked (testing for false positives).
- Analysis: The test validates whether DLP policies, triggered by accurate classification labels, are correctly enforced across critical data exfiltration vectors.
Workflow and System Diagrams
Diagram 1: Data Security Pipeline
Diagram 2: Leak Detection Logic
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Tools for Data Security Benchmarking Experiments
| Tool / Reagent | Function | Application in Research Context |
|---|---|---|
| AI-Powered Classification Tool (e.g., Numerous.ai, Concentric AI) | Automatically discovers, identifies, and labels sensitive data using context-aware AI [48] [46]. | Foundation for accurately tagging research data, clinical trial information, and patient records prior to applying security controls. |
| Data Loss Prevention (DLP) Solution (e.g., Symantec, Microsoft) | Monitors, detects, and blocks sensitive data while in use, in motion, or at rest [49] [50]. | The enforcement mechanism in experiments, used to test policies that prevent exfiltration of classified research data. |
| Cloud-Based Leak Test Apparatus | Automated systems for integrity testing, often used in pharmaceutical packaging [51]. | Analogous tool for validating the integrity of data "containers" and ensuring no silent failures in data protection systems. |
| Synthetic Test Dataset | A curated collection of files and data records with known sensitivity labels. | Serves as the controlled "reagent" for benchmarking classification accuracy and DLP efficacy without using live production data. |
Validation and Comparison: Ensuring scFM Model Performance is Real and Actionable
Frequently Asked Questions
What is data leakage in the context of scFM benchmarking? Data leakage occurs when information from the evaluation dataset is unintentionally used during a model's construction phase (e.g., pre-training). This can lead to an overestimation of the model's true capabilities on benchmark tasks, as it is being tested on data it has already seen, rather than on its ability to generalize to new, unseen data [38] [52].
Why is it a critical issue for single-cell foundation models? Data leakage compromises the validity of benchmark studies, which are essential for guiding biological and clinical research. If a model's performance is inflated due to leakage, it can mislead researchers into selecting an inferior model for crucial applications like cell atlas construction, tumor microenvironment studies, or treatment decision-making [7]. Furthermore, benchmarking studies have shown that simple baseline models can sometimes perform comparably to complex scFMs, making it vital to ensure that evaluations are not biased by leakage [7] [53].
How can I check if my benchmark dataset has been leaked? Detecting leakage can be challenging, especially with closed-source models. A proposed method involves:
- Synthesizing a Reference Benchmark: Create a paraphrased version of your original benchmark that maintains its format and difficulty but uses different surface text [52] [54].
- Calculating Metrics: Evaluate the model of interest on both the original and synthesized benchmarks using metrics like Perplexity and N-gram Accuracy [52] [54].
- Analyzing Discrepancies: A significantly better performance (e.g., lower perplexity, higher n-gram accuracy) on the original benchmark compared to the synthesized one suggests the model may have been exposed to the original data during training [52] [54].
What are some best practices for preventing data leakage in my study?
- Curate Pre-training Data: Maintain meticulous records of the sources and contents of your pre-training data. If possible, screen it against planned evaluation benchmarks [38].
- Use Leakage-Free Benchmarks: Whenever available, use curated benchmarks from which known leaked samples have been removed, such as the proposed
LessLeak-Benchfor software engineering, adapted for biological data [38]. - Promote Transparency: Document and disclose the relationship between pre-training data and evaluation benchmarks using a Benchmark Transparency Card or similar framework [52].
- Employ Rigorous Evaluation Frameworks: Use frameworks like Systema that are specifically designed to control for systematic biases and focus on perturbation-specific effects, which helps mitigate the risk of evaluating on confounded signals [53].
My scFM performs well on standard metrics but fails in real-world applications. Why? This is a classic sign that standard evaluation metrics might be susceptible to systematic variation—consistent technical or biological biases in the dataset (e.g., batch effects, cell cycle differences between perturbed and control cells). Your model may be learning these systematic shifts rather than the underlying biology of interest. Employing more robust evaluation frameworks that control for these confounders is essential [53].
Troubleshooting Guides
Problem: Inflated Performance on Perturbation Prediction
Symptoms: Your scFM achieves high scores on metrics like Pearson correlation (PearsonΔ) when predicting transcriptional responses to genetic perturbations, but simple baselines (e.g., predicting the average expression of all perturbed cells) perform just as well [53] [2].
Diagnosis: The model is likely capturing systematic variation instead of perturbation-specific effects. Systematic variation arises from consistent differences between control and perturbed cell populations due to factors like selection bias in the perturbation panel or confounding biological processes (e.g., widespread cell-cycle arrest) [53].
Solution: Implement the Systema evaluation framework to disentangle true predictive performance from systematic biases [53].
- Experimental Protocol:
- Quantify Systematic Variation: For your perturbation dataset, use Gene Set Enrichment Analysis (GSEA) and tools like AUCell to identify pathways that are systematically different between all perturbed and all control cells.
- Re-evaluate with Control Metrics: Compare your scFM against simple baselines like the "perturbed mean" (average expression profile of all perturbed cells) or "matching mean" (for combinatorial perturbations). A lack of significant improvement over these baselines indicates that performance is driven by systematic effects.
- Focus on Perturbation-Specific Effects: Systema emphasizes the model's ability to reconstruct the unique landscape of individual perturbations, not just the average treatment effect.
The following workflow outlines the steps for a rigorous, leakage-conscious benchmarking study of scFMs:
Problem: Unclear Model Selection for a Specific Task
Symptoms: You need to choose an scFM for a particular downstream task (e.g., cell type annotation on a novel dataset), but benchmark rankings are inconsistent, and no single model dominates all others [7].
Diagnosis: Model performance is highly dependent on the specific task, dataset size, and biological context. A one-size-fits-all approach does not work for scFMs [7].
Solution: Use a multi-faceted evaluation approach that goes beyond aggregate performance scores.
- Experimental Protocol:
- Task-Specific Ranking: Consult benchmarks that provide rankings for your specific task of interest (e.g., cell-level vs. gene-level tasks) [7].
- Evaluate Biological Coherence: Use novel, biology-aware metrics to assess the model's insights.
- scGraph-OntoRWR: Measures whether the relationships between cell types captured by the scFM's embeddings are consistent with known biological knowledge from cell ontologies [7].
- Lowest Common Ancestor Distance (LCAD): For cell type annotation, this metric assesses the severity of misclassification by measuring the ontological proximity between the predicted and true cell type. A smaller LCAD indicates a less severe error [7].
- Consider Dataset Properties: Use the Roughness Index (ROGI) as a proxy to predict how well a model might perform on your specific dataset. A smoother landscape in the latent space often correlates with better downstream task performance [7].
The table below summarizes key findings from recent large-scale benchmarking studies relevant to scFM evaluation, highlighting performance comparisons and data leakage impacts.
| Benchmark Focus | Key Finding | Quantitative Result | Implication for scFM Evaluation |
|---|---|---|---|
| scFM Performance [7] [53] [2] | Simple baselines can match complex scFMs on perturbation prediction. | Perturbed mean baseline outperformed or matched scFMs on unseen one-gene perturbations across all datasets in one study [53]. | Highlights the need for metrics that discern true biological learning from capturing average effects. |
| Data Leakage Impact [38] | Performance is significantly inflated on leaked data samples. | On the APPS benchmark, an LLM's Pass@1 score was 4.9x higher on leaked vs. non-leaked samples [38]. | Underscores that even small leakage can drastically skew results, necessitating leakage checks. |
| Data Leakage Prevalence [38] | Leakage is minimal on average but severe for specific benchmarks. | Average leakage ratios were 4.8% (Python), 2.8% (Java), and 0.7% (C/C++), but QuixBugs had a 100% leakage ratio [38]. | Researchers must be aware that some popular benchmarks are highly susceptible to leakage. |
The Scientist's Toolkit: Research Reagent Solutions
This table lists essential components and their functions for conducting a rigorous scFM benchmarking study.
| Item / Reagent | Function in Evaluation |
|---|---|
| Systema Framework [53] | An evaluation framework that controls for systematic variation and focuses on a model's ability to predict perturbation-specific effects, providing a more biologically meaningful performance readout. |
| scGraph-OntoRWR Metric [7] | A novel metric that evaluates the biological relevance of scFM embeddings by measuring the consistency of captured cell-type relationships with prior knowledge from cell ontologies. |
| LessLeak-Bench Principle [38] | The methodology for creating a benchmark from which known leaked samples have been removed. This principle should be applied to scFM benchmarks to ensure fair evaluation. |
| Perturbed Mean Baseline [53] | A simple non-parametric baseline (average expression profile of all perturbed cells) that serves as a critical sanity check for evaluating perturbation prediction tasks. |
| Benchmark Transparency Card [52] | A documentation framework to clearly report the relationship between a model's pre-training data and evaluation benchmarks, promoting transparency and reproducibility. |
| Roughness Index (ROGI) [7] | A proxy measure that correlates model performance with the smoothness of the cell-property landscape in the pretrained latent space, aiding in dataset-specific model selection. |
Methodology for Detecting Data Leakage
The following diagram and protocol detail the steps for implementing a data leakage detection pipeline, adapted from LLM research to the context of scFMs.
- Step 1: Preparation. For the benchmark dataset in question, use a language model (e.g., ChatGPT) to create several (e.g., three) synthetically paraphrased versions. These versions should preserve the logical structure and difficulty of the original tasks but alter the surface text [52] [54].
- Step 2: Metric Calculation. Evaluate the scFM (or its associated tokenizer/embedder) on both the original benchmark (
D_original) and the synthesized benchmarks (D_synthetic). Calculate the following metrics for both:- Perplexity: Quantifies how well the model predicts a sequence. Lower perplexity indicates higher confidence and potential familiarity with the data. It is often calculated on the "answer" part of a sample [52] [54].
- N-gram Accuracy: Checks the model's ability to predict exact subsequences of tokens. If a model correctly predicts the majority of n-grams in a sample, it may have memorized it during training [52] [54]. Average the metrics across the synthesized versions to get a stable reference value.
- Step 3: Comparison. Calculate the metric decrement for the training split (
Δ_train) and the test split (Δ_test), whereΔ = Metric_original - Metric_synthetic. Then, compute the relative percentage decreaseδ = (Δ / Metric_synthetic) * 100. The key is to find the disparity:δ_train-test = δ_train - δ_test[52] [54]. - Step 4: Judgment. A significant positive
δ_train-testdisparity suggests that the model is disproportionately more familiar with the training split than the test split, indicating potential leakage of the benchmark's training data [52] [54]. A value near zero suggests either no leakage or equal leakage of both splits.
Comparative Analysis of ML Models in Leakage-Free Environments
Frequently Asked Questions
Q1: What is data leakage and why is it a critical issue in benchmarking single-cell foundation models (scFMs)?
Data leakage occurs when information from outside the training dataset, such as from the test set, inadvertently influences the model during its training phase [55] [56]. This leads to overly optimistic performance estimates because the model is effectively "cheating" by gaining access to information it should not have prior to evaluation [57]. In the context of scFM benchmarking, this compromises the validity of comparative analyses, as a model may appear superior due to leaked information rather than genuine learning and generalization capability [56]. This can result in models that perform poorly when deployed in real-world scenarios, such as predicting drug responses or identifying novel cell types in a clinical setting [55] [57].
Q2: What are the common signs that my scFM benchmark may be suffering from data leakage?
Several indicators can signal potential data leakage [55] [58]:
- Unusually High Performance: Your model shows exceptionally high accuracy or other performance metrics that seem "too good to be true" [55] [58].
- Significant Performance Discrepancy: The model performs excellently on the training or validation sets but poorly on a truly held-out test set or new, unseen data [55] [57].
- Inconsistent Cross-Validation Results: Large variations in performance metrics across different folds of cross-validation may indicate improper data splitting and leakage between folds [55] [56].
Q3: During which stages of the scFM pipeline is data leakage most likely to occur?
Data leakage can infiltrate various stages of the machine learning pipeline [55] [56]:
- Data Preprocessing: Applying steps like normalization, scaling, or imputation to the entire dataset before splitting it into training and test sets. These operations must be fit on the training data only and then applied to the test data [55] [59].
- Feature Engineering: Creating features using information from the entire dataset, including the test set, or including features that would not be available at the time of prediction (target leakage) [55] [56].
- Incorrect Data Splitting: Improperly splitting data, especially time-series or data with repeated measurements from the same subject, can lead to future data or data from the same subject appearing in both training and test sets [55] [57].
Q4: How can a structured benchmark, like PertEval-scFM, help in the leakage-free evaluation of scFMs?
Standardized benchmarking frameworks such as PertEval-scFM are specifically designed to provide a rigorous and controlled environment for evaluating models [3]. By implementing strict protocols for data partitioning and preprocessing, these frameworks help mitigate the risk of data leakage. They ensure that all models are assessed on a level playing field using a consistent and leakage-free test set, which is crucial for obtaining fair and comparable performance metrics [3] [37].
Q5: What are the practical implications of data leakage for drug development professionals using scFMs?
For professionals in drug development, data leakage can have severe consequences [55] [57]. A model compromised by leakage may fail to accurately predict a drug's efficacy or a patient's sensitivity in a clinical trial, leading to misguided decisions, wasted resources, and failed treatments [55]. Ensuring leakage-free models is therefore not just a technical necessity but a critical step in developing reliable tools for precision medicine and treatment decision-making [37].
Experimental Protocols for Leakage-Free Benchmarking
Protocol 1: Rigorous Data Partitioning for scFM Evaluation
Objective: To create training, validation, and test sets that prevent information leakage, ensuring a fair evaluation of model generalizability.
Methodology:
- Initial Holdout: Before any exploratory data analysis or preprocessing, set aside a final test set. This data must remain completely untouched and unseen until the final evaluation stage [55] [58].
- Temporal and Subject-Aware Splitting: For datasets with temporal dimensions or multiple samples from the same subject, ensure that the split respects the time order and subject identity. No data from the future should be used to predict the past, and no data from the same subject should appear in both training and test sets [55] [57].
- Stratified Splitting: When dealing with imbalanced datasets (e.g., rare cell types), use stratified splitting to maintain the proportional distribution of key labels (like cell type) across the training, validation, and test sets.
- Nested Cross-Validation: For hyperparameter tuning and model selection, use a nested cross-validation setup [56]. An inner loop is used for tuning parameters on the training fold, while an outer loop provides an unbiased performance estimate. This prevents the validation data from influencing the model selection process.
Protocol 2: Preprocessing in a Leakage-Aware Manner
Objective: To perform necessary data preprocessing without leaking information from the test set into the training process.
Methodology:
- Fit on Training, Transform on Test: All preprocessing steps (e.g., normalization, handling missing values, feature selection) must be computed using parameters (like mean and standard deviation) derived exclusively from the training set [55] [59].
- Pipeline Construction: Implement these steps within a machine learning pipeline that encapsulates the preprocessing and model training. This ensures that when the model is applied to the validation or test set, the same training-derived parameters are used for transformation [59].
- Independent Application: Apply the fitted preprocessors from the training set to the validation and test sets independently, without any refitting.
Protocol 3: Implementing a Zero-Shot Evaluation Framework
Objective: To assess the intrinsic biological knowledge captured by an scFM during pre-training without any task-specific fine-tuning, thereby eliminating a major source of leakage.
Methodology:
- Embedding Extraction: Use the pre-trained scFM (without further training) to generate latent representations (embeddings) for cells or genes from a held-out benchmark dataset [37].
- Simple Downstream Model: Train a simple, shallow model (e.g., a linear classifier or logistic regression) on these extracted embeddings to perform a specific downstream task (e.g., cell type annotation or perturbation prediction) [3] [37].
- Performance Assessment: Evaluate the performance of this simple model on the unseen test set. Strong performance indicates that the scFM embeddings contain meaningful, generalizable biological information, while poor performance suggests limitations in the foundation model's pre-training [3] [37].
Quantitative Benchmarking Data
Table 1: Performance Comparison of scFMs vs. Baselines on Key Tasks (Example Findings from Benchmarks)
| Model Category | Model Name | Cell Type Annotation (Accuracy) | Perturbation Prediction (Performance) | Batch Integration (ASW Score) | Data Leakage Risk |
|---|---|---|---|---|---|
| Single-Cell Foundation Models (scFMs) | scGPT | Variable [37] | Limited improvement in zero-shot [3] | High [37] | Low (if pre-trained correctly) |
| Geneformer | Variable [37] | Limited improvement in zero-shot [3] | High [37] | Low (if pre-trained correctly) | |
| Traditional ML Baselines | Seurat | Context-dependent [37] | N/A | High [37] | Moderate (requires careful splitting) |
| scVI | Context-dependent [37] | N/A | High [37] | Moderate (requires careful splitting) | |
| HVGs + Logistic Regression | Can outperform scFMs on specific datasets [37] | N/A | N/A | Low |
Table 2: Impact of Different Data Leakage Types on Model Performance [57]
| Type of Data Leakage | Impact on Model Performance | Common Cause |
|---|---|---|
| Feature Selection Leakage | Inflates performance, creates significant false positives [57] | Selecting features based on the entire dataset before training/test split. |
| Repeated Subject Leakage | Inflates performance, model memorizes individuals [57] | Data from the same subject appears in both training and test sets. |
| Preprocessing Leakage | Inflates performance, test data influences training [55] | Normalizing data using global mean/std from train and test sets combined. |
| Temporal Leakage | Inflates performance, model uses future to predict past [55] | Using future data points to train a model for predicting past events. |
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Tools for Leakage-Free scFM Benchmarking
| Tool / Resource Name | Type | Function in Research | Relevance to Leakage Prevention |
|---|---|---|---|
| PertEval-scFM [3] | Benchmarking Framework | Standardized evaluation of scFMs for perturbation prediction. | Provides a rigorous, predefined test bed to avoid inadvertent leakage during experimental setup. |
| scGraph-OntoRWR [37] | Evaluation Metric | Measures consistency of cell type relationships with prior biological knowledge. | Offers a biology-grounded assessment less susceptible to being gamed by leaked features. |
| CellxGene [20] [37] | Data Platform | Provides unified access to annotated single-cell datasets. | Source of high-quality, standardized data; using curated public data reduces risks from in-house processing errors. |
| Scikit-learn Pipelines [59] | Programming Tool | Encapsulates preprocessing and model steps into a single object. | Ensures preprocessing is fit only on training data, a primary defense against preprocessing leakage [55] [59]. |
| AIDA v2 Dataset [37] | Independent Dataset | Provides a completely unseen, unbiased dataset for final validation. | Serves as a gold standard for a final, leakage-free test of model generalizability after all development. |
Workflow and Relationship Visualizations
Diagram 1: A high-level workflow for preventing data leakage in ML model benchmarking. The critical steps are the initial holdout of the test set and ensuring all preprocessing is derived from the training data.
Diagram 2: The zero-shot evaluation protocol for single-cell foundation models. This method assesses the intrinsic knowledge within the scFM without fine-tuning, minimizing the risk of data leakage during the benchmarking process.
Troubleshooting Guides
Guide 1: Diagnosing and Remediating Data Leakage in scFM Benchmarking Pipelines
Problem: After implementing a new single-cell foundation model (scFM), its benchmarked performance on perturbation prediction tasks appears suspiciously high and fails to generalize in real-world validation.
Diagnosis: This is a classic symptom of data leakage, where information from the test set is inadvertently used during the model training process. This invalidates the benchmark results by creating an over-optimistic performance estimate [26].
Solution: A step-by-step remediation protocol.
| Step | Action | Expected Outcome |
|---|---|---|
| 1. Audit Data Flow | Trace the entire pipeline to ensure no pre-processing (e.g., normalization, feature selection, covariate correction) is applied to the combined dataset before train/test splitting [26]. | Identification of the exact stage where leakage is introduced. |
| 2. Isolate Perturbations | Re-split data so that no specific perturbation condition (e.g., a particular gene knockout) is present in both training and test sets [60]. | A valid assessment of the model's ability to generalize to novel perturbations. |
| 3. Implement Strict CV | For cross-validation, ensure all steps (feature selection, hyperparameter tuning) are performed within each training fold, without access to the held-out validation fold [26]. | A robust, non-leaky performance estimate. |
| 4. Re-run Benchmark | Execute the cleaned pipeline and compare the new performance metrics (e.g., MSE, Spearman correlation) against the previous, leaky results. | A drop in performance, yielding a more realistic and reproducible benchmark. |
Guide 2: Resolving "Illusory Success" in Perturbation Effect Prediction
Problem: Your model perfectly predicts that a knocked-down gene will have lower expression, but fails to predict the downstream effects on other genes accurately.
Diagnosis: This is known as "illusory success" [60]. The model is leveraging the direct, trivial connection between the intervention and the targeted gene, which does not reflect genuine biological insight into the regulatory network.
Solution: Implement a hold-out strategy for directly perturbed genes.
Protocol:
- Baseline Establishment: Begin predictions from the average expression profile of all control samples [60].
- Input Manipulation: For a perturbation (e.g., knockout), set the expression of the targeted gene to zero in the input vector. For overexpression, set it to the observed post-intervention value [60].
- Target Omission: When training the model to predict the expression of a specific gene j, exclude all samples where gene j was the direct target of the perturbation [60]. This forces the model to learn the regulatory relationships between genes, not just the direct intervention effect.
Frequently Asked Questions (FAQs)
Q1: What is data leakage in the specific context of benchmarking scFMs? Data leakage occurs when information from the benchmark's test dataset unintentionally influences the training of the model. This breaches the fundamental principle of keeping training and test data separate, leading to inflated and non-reproducible performance metrics that do not reflect the model's true ability to generalize [26]. In scFM benchmarking, this often happens when pre-processing is done on the entire dataset before splitting, or when the same perturbation conditions appear in both training and test sets [60].
Q2: Why is my scFM's benchmark performance so much higher than traditional models? Could this be valid? While it is possible for a superior model to achieve higher performance, a significant and unexpected performance gap is a major red flag for data leakage. Empirical studies have shown that leakage can drastically inflate performance, especially for prediction tasks with initially weak baseline performance [26]. It is crucial to validate this result by checking for leakage and ensuring the benchmark follows a strict, contamination-free protocol like those used in frameworks such as AntiLeakBench [32] or PertEval-scFM [2].
Q3: How does data leakage actually affect my numerical results? The impact of leakage is not uniform; it depends on the type of leakage and the baseline performance of the task. The table below summarizes empirical findings from a connectomics study, which provides a quantitative analogy for scFM benchmarking [26].
Table 1: Quantitative Impact of Different Leakage Types on Model Performance
| Leakage Type | Description | Impact on Weak Baseline Task | Impact on Strong Baseline Task |
|---|---|---|---|
| Feature Leakage | Feature selection performed on combined train/test data. | Drastic inflation (e.g., +0.47 in correlation) | Minor inflation (e.g., +0.03 in correlation) |
| Subject Leakage | Duplicated subjects or non-independent data splits. | Large inflation (e.g., +0.28 in correlation) | Moderate/Minor inflation (e.g., +0.04 in correlation) |
| Covariate Leakage | Covariate correction applied before data splitting. | Can decrease performance (e.g., -0.06 in correlation) | Minor decrease (e.g., -0.02 in correlation) |
Q4: What is the difference between a data leak and a data breach? This is a critical distinction. In a cybersecurity context, a data leak is often an accidental exposure of sensitive data, while a data breach is the result of a deliberate cyberattack to steal data [61]. In machine learning benchmarking, the concept is analogous: a "leak" is the unintentional seepage of test set information into the training process, whereas a "breach" would be a deliberate violation of benchmarking rules.
Q5: Are there standardized tools to help prevent data leakage in my benchmarks? Yes, the field is moving towards automated and standardized frameworks to combat this issue.
- AntiLeakBench: A framework designed to automatically construct benchmarks using explicitly new knowledge absent from model training sets, ensuring a strictly contamination-free evaluation [32].
- PertEval-scFM: A standardized framework for evaluating perturbation effect prediction in single-cell biology, which includes careful data splitting to prevent leakage [2].
- BioLLM: A unified system that provides standardized APIs for integrating and benchmarking scFMs, helping to reduce inconsistencies that can lead to leakage [13].
Experimental Protocols for Leakage-Free Benchmarking
Protocol 1: Implementing a Strict Train-Test Split for Novel Perturbation Prediction
Objective: To fairly evaluate a model's ability to predict outcomes of unseen genetic perturbations.
Methodology:
- Data Pooling: Aggregate your perturbation transcriptomics dataset (e.g., from Perturb-seq).
- Condition-Based Splitting: Randomly allocate distinct perturbation conditions (e.g., gene A knockdown, gene B overexpression) and all control samples to the training set. A separate, mutually exclusive set of perturbation conditions is allocated to the test set [60].
- Input/Output Setup:
- Training: Models are trained to predict gene expression from regulator expression, omitting samples where a gene was directly perturbed during its own prediction task [60].
- Testing: Start from the control expression profile. For a test perturbation (e.g., knockout of gene X), set its input expression to 0. The model then predicts the expression of all other genes [60].
Visual Workflow:
Protocol 2: Cross-Validation with Nested Pre-processing
Objective: To obtain a reliable performance estimate via cross-validation without leakage from feature selection or hyperparameter tuning.
Methodology:
- Outer Loop: Split the entire dataset into k folds.
- Inner Loop: For each of the k training folds, perform all pre-processing steps (e.g., feature selection, hyperparameter optimization) using only that training fold. This often involves another layer of cross-validation within the training fold.
- Validation: Train a model on the pre-processed training fold and evaluate it on the held-out outer test fold. Repeat for all k folds [26].
Visual Workflow:
Table 2: Key Solutions for Robust scFM Benchmarking
| Resource / Reagent | Function / Description | Example / Source |
|---|---|---|
| Anti-Leakage Benchmarks | Provides automatically constructed, contamination-free benchmarks using post-cutoff knowledge to prevent test data from being in training sets. | AntiLeakBench [32] |
| Standardized Evaluation Frameworks | Offers a unified interface and APIs for consistent model integration, switching, and evaluation, reducing implementation errors. | BioLLM [13], PertEval-scFM [2] |
| Strict Data Splitting Protocols | Methodologies for ensuring no perturbation condition overlaps between training and test data, crucial for evaluating generalizability. | PEREGGRN's non-standard data split [60] |
| High-Quality, Curated Datasets | Expertly curated, rich, and current data capturing decades of interventional trials, providing an unbiased view for benchmarking. | Intelligencia.ai's Dynamic Benchmarks [62] |
| Dynamic Benchmarking Platforms | Solutions that incorporate new data in near real-time and offer advanced filtering based on ontology, modality, and disease for precise comparisons. | Intelligencia AI [62] |
The Role of External Validation Sets and Blind Trials
Frequently Asked Questions
Q1: What is the fundamental purpose of an external validation set in model development? A1: An external validation set is used to assess how a predictive model will perform on data sources that were not used during its training. This process, known as external validation, is a critical step for verifying model transportability across different types of healthcare facilities, geography, and patient populations. Without it, model performance may deteriorate significantly when applied in real-world, external settings [63].
Q2: Our model performs well on internal validation data but fails on external data. What are the primary causes? A2: This common issue often stems from data leakage or a lack of generalizability. Key causes include:
- Cohort Shift: The internal and external populations have different underlying characteristics (e.g., age distribution, prevalence of outcomes). For instance, a model trained on a general adult population may fail on a cohort comprised mostly of elderly patients [63].
- Inadequate Blinding: If the team is not blinded to the data partition during experiments, it can lead to unconscious bias in model tuning, making it overfit to the internal validation set.
- Feature Discrepancies: The optimization algorithm may fail to find appropriate weights if the external data contains features or statistical relationships not present or differently represented in the internal cohort [63].
Q3: How can we prevent data leakage in our benchmarking workflow? A3: Preventing data leakage requires a combination of procedural and technical measures [64]:
- Strict Protocols: Implement and enforce access controls and clear documentation practices for data handling.
- Blinded Trials: Ensure that researchers involved in model development and tuning are blinded to the composition of the external validation sets.
- Process Automation: Use automated scripts for data partitioning to prevent manual errors or cherry-picking of data.
- Audit Trails: Maintain secure, validated electronic systems that record data access and changes.
Q4: What are the ALCOA+ principles and how do they relate to data integrity in benchmarking? A4: ALCOA+ is a framework essential for ensuring data integrity in regulated research. The principles are [65]:
- Attributable: Who generated the data and when?
- Legible: Is the data readable and permanently recorded?
- Contemporaneous: Was it recorded at the time of the activity?
- Original: Is it the source record or a certified copy?
- Accurate: Is it error-free and reflects actual observations?
- Complete: Is all data included, with nothing omitted?
- Consistent: Is the data self-consistent over time?
- Enduring: Is it preserved for the required lifetime?
- Available: Can it be accessed for review and inspection?
Q5: A method failed to estimate external performance from summary statistics. Why might this happen? A5: The weighting method that estimates external performance can fail if certain external statistics cannot be represented as a weighted average of the internal cohort's features. For example, if an external dataset includes a proportion of subjects under 20 years old, but the internal cohort (like MDCR) has zero individuals in that age group, then no set of weights can reproduce that statistic. The success of the method depends on the provided statistics and the feasibility of the optimization problem [63].
Troubleshooting Guides
Issue 1: Poor Model Performance on External Validation Sets
| Symptom | Potential Cause | Corrective Action |
|---|---|---|
| Significant drop in AUROC/Accuracy on external data. | Cohort shift or population differences. | Benchmark using diverse data sources. Use multiple heterogeneous data sources during development to test robustness [63]. |
| Model calibration is poor on new datasets. | Overfitting to internal data characteristics. | Incorporate external summary statistics early. Use methods that re-weight the internal cohort to match external statistics during development, not just at the final validation stage [63]. |
| Inconsistent performance across patient subgroups. | Model did not learn generalizable features. | Apply rigorous blinding. Blind the research team to the external validation set to prevent biased model selection and tuning. |
Issue 2: Suspected Data Leakage in scFM Benchmarking Pipeline
| Symptom | Potential Cause | Corrective Action |
|---|---|---|
| Unrealistically high performance on the "validation" set. | Features from the external set inadvertently used in training. | Implement data leakage prevention tools. Use technical measures to monitor and prevent unauthorized data transfers between partitioned datasets [64]. |
| Audit trail shows access to test data by development team. | Failure to enforce access control policies. | Establish clear documentation practices. Define and follow Standard Operating Procedures (SOPs) for data entry, storage, and retrieval for all experiments [65]. |
| Inability to reproduce benchmarking results. | Lack of a controlled, enduring data environment. | Conduct routine audits. Regularly review data management practices to identify and rectify potential weaknesses in the pipeline [65]. |
Quantitative Data from External Validation Benchmarking
The following data is synthesized from a large-scale benchmarking study that trained prediction models on an internal data source and validated them on external ones. The study used metrics like AUROC (Area Under the Receiver Operating Characteristic curve) to measure discrimination, Calibration-in-the-large for calibration, and Brier scores for overall accuracy [63].
Table 1: Example External Validation Performance for a Diarrhea Prediction Model
| Data Source (Internal) | Internal AUROC | External Data Source | Actual External AUROC | Estimated External AUROC |
|---|---|---|---|---|
| CCAE | 0.610 | MDCR | 0.587 | 0.585 [63] |
Table 2: Error Percentiles in Estimating External Performance Metrics
| Performance Metric | 95th Error Percentile in Estimation |
|---|---|
| AUROC (Discrimination) | 0.03 [63] |
| Calibration-in-the-large | 0.08 [63] |
| Brier Score (Overall Accuracy) | 0.0002 [63] |
| Scaled Brier Score | 0.07 [63] |
This methodology estimates model performance on an external data source using only summary-level statistics, without requiring access to the underlying patient-level data [63].
- Model Training: Train your predictive model on the full internal cohort.
- Acquire External Statistics: Obtain summary statistics from the target external data source. These statistics should characterize the target population (e.g., demographic distributions, outcome prevalence).
- Weight Calculation:
- The method seeks to assign weights to each unit in the internal cohort.
- The objective is to find a set of weights such that when the internal cohort is re-weighted, its summary statistics closely match the provided external statistics.
- Performance Estimation:
- Apply the calculated weights to the internal cohort.
- Compute the desired performance metrics (e.g., AUROC, calibration) using the true labels and model predictions from this weighted internal cohort.
- These metrics serve as the estimate for the model's performance on the external data.
Validation: This method has been benchmarked by treating one data source as internal and others as external, showing accurate estimations with low error percentiles (see Table 2) [63].
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Components for a Robust Benchmarking Research Pipeline
| Item | Function / Explanation |
|---|---|
| Multiple Heterogeneous Data Sources | Provides the foundation for meaningful external validation. Using five large US data sources, a benchmark study demonstrated how performance varies across populations [63]. |
| Data Leakage Prevention (DLP) Tools | Intrusive software that monitors and prevents unauthorized transfer of sensitive data between partitions (e.g., from test set to training set), enforcing protocol adherence [64]. |
| Electronic Lab Notebook (ELN) | A validated electronic system for recording experimental procedures and data, supporting ALCOA+ principles by ensuring data is Attributable, Legible, and Contemporaneous [65]. |
| OHDSI/OMOP CDM Infrastructure | A global, collaborative network and a common data model that standardizes data structure and semantics, significantly reducing the burden of harmonizing data across sources for external validation [63]. |
| Statistical Weighting Algorithm | The core method that calculates weights for internal data points to mimic external summary statistics, enabling performance estimation without data sharing [63]. |
Experimental Workflow and Data Partitioning Diagram
The following diagram illustrates the core workflow for conducting a blinded trial with external validation, highlighting the critical points for data leakage prevention.
Data Leakage Prevention Signaling Pathway
This diagram visualizes the logical relationships between security controls, potential failure points, and outcomes in a data integrity system, based on standards like ISO 27002:2022 Control 8.12 [64].
Frequently Asked Questions
What does "zero-shot embedding" mean in the context of scFMs? Zero-shot embedding refers to the direct use of a model's data representation (for a gene or cell) without any additional training or fine-tuning for a specific task. This allows researchers to leverage the general biological knowledge the model learned during its large-scale pretraining for immediate analysis [7].
Why is my scFM model performing poorly on a specific cancer type? No single scFM consistently outperforms others across all tasks or biological contexts. Performance is influenced by factors like the model's original pretraining data, the specific task (e.g., cell annotation vs. drug sensitivity prediction), and the complexity of the dataset. You may need to select a different model tailored to your specific cancer type and experimental question [7].
What is data leakage in benchmarking, and how can I prevent it? Data leakage occurs when information from the test dataset unintentionally influences the training process, leading to overly optimistic and non-reproducible performance estimates. To prevent this, ensure complete separation between training and test sets, avoiding any overlap in patients, samples, or time-series data points. Using publicly available, pre-processed benchmark datasets created with leakage prevention in mind is a recommended best practice [8].
How can we quantitatively measure if an scFM has learned meaningful biology? Beyond standard performance metrics, novel ontology-informed metrics have been developed. For example, the scGraph-OntoRWR metric evaluates whether the relationships between cell types captured by the model's embeddings are consistent with established biological knowledge from cell ontologies [7].
Troubleshooting Guides
Issue 1: Inconsistent Cell Type Annotation Results
Problem: Your scFM model produces different or inaccurate cell type labels when analyzing the same cell population across different experiments or datasets.
Investigation and Solutions:
- Understand the Problem: Check if the inaccuracies are random or systematically confuse biologically similar cell types (e.g., confusing CD4+ T-cells with CD8+ T-cells). The latter might be less severe and indicates the model has learned some hierarchy [7].
- Isolate the Issue:
- Compare to a baseline: Run a well-established method like Seurat or Harmony on your dataset for comparison [7].
- Check dataset compatibility: Verify that the cell types in your dataset were represented in the model's pretraining data. Models struggle with novel cell types not seen during pretraining.
- Reproduce the issue: Confirm the inconsistency is reproducible by testing the model on a controlled, high-quality benchmark dataset.
- Find a Fix or Workaround:
- Solution A (Workaround): Use the scFM's embeddings as a high-quality input for a simpler, traditional classifier that you train on a small, well-annotated portion of your specific data [7].
- Solution B (Model Selection): Switch to an scFM that demonstrated superior performance in cell type annotation tasks in benchmark studies. Holistic rankings from benchmarks can guide this choice [7].
- Solution C (Leverage Biological Knowledge): Use metrics like the Lowest Common Ancestor Distance (LCAD) to understand if misclassifications are at least biologically plausible, which can help you manually curate and validate the results [7].
Issue 2: Suspected Data Leakage in Experimental Setup
Problem: Your model shows exceptionally high performance during validation but fails to generalize to new, independent data, suggesting the benchmark results may be biased.
Investigation and Solutions:
- Understand the Problem: Review your data splitting procedure. Data leakage is a particular challenge in predictive process monitoring and can make results impossible to reproduce [8].
- Isolate the Issue:
- Audit your data splits: Ensure no single patient, sample, or time-series event is represented in both the training and test sets.
- Check for temporal leakage: For time-series data, ensure all data from a specific date or patient visit is entirely in either the training or test set, not split between them.
- Review preprocessing: Confirm that normalization or feature selection was applied independently to the training set before being applied to the test set.
- Find a Fix or Workaround:
- Solution A (Adopt Principled Datasets): Use public benchmark datasets specifically designed with data leakage prevention in mind [8].
- Solution B (Re-split Data): Implement a more rigorous splitting strategy, such as grouping all data by patient ID before splitting to ensure complete patient-level separation.
- Solution C (Independent Validation): Always validate your final model on a completely new, external dataset that was not used in any part of the model development or selection process.
Issue 3: Poor Generalization from Preclinical to Clinical Models
Problem: A model trained on preclinical data (e.g., cell lines, animal models) does not accurately predict human clinical outcomes, hindering the "bench-to-bedside" translation.
Investigation and Solutions:
- Understand the Problem: This is a core challenge in translational science. The goal is to "reverse translate" clinical insights to inform model development [66].
- Isolate the Issue:
- Identify the gap: Determine if the failure is due to pharmacological differences (e.g., target binding), physiological differences, or different disease mechanisms between models and humans.
- Gather relevant data: Integrate all available clinical data, including pharmacokinetic/pharmacodynamic (PK/PD) profiles and real-world evidence, to understand the clinical context better [66].
- Find a Fix or Workaround:
- Solution A (Quantitative Modeling): Use model-based meta-analysis (MBMA) to characterize the dose-response and longitudinal effects of existing therapies, creating a knowledge-based framework for new compounds [66].
- Solution B (QSP/PBPK Modeling): Employ Quantitative Systems Pharmacology (QSP) or Physiologically Based Pharmacokinetic (PBPK) models. These platforms integrate preclinical and clinical data to mechanistically simulate disease pathways and drug effects in humans, helping to bridge the translational gap [66].
- Solution C (Incorporate Clinical Champions): Engage clinical champions and adopters who understand both the biological and clinical dimensions to help refine the model's objectives and ensure it addresses a real clinical need [67].
Experimental Protocol for scFM Benchmarking
The following table summarizes the key methodological steps for a robust benchmark of single-cell foundation models, as derived from current research [7].
- Table 1: scFM Benchmarking Experimental Protocol
| Protocol Step | Description | Key Parameters & Considerations |
|---|---|---|
| 1. Model Selection | Include a diverse set of scFMs with different architectures & pretraining strategies. | Models: Geneformer, scGPT, scFoundation, etc. Consider: Model size (parameters), pretraining data, input gene handling [7]. |
| 2. Task Definition | Evaluate models on a range of gene-level and cell-level tasks. | Tasks: Batch integration, cell type annotation, cancer cell ID, drug sensitivity prediction. Aim for clinical relevance [7]. |
| 3. Data Curation | Use multiple, high-quality datasets with known labels. Introduce an independent validation set. | Ensure: Dataset diversity (tissues, conditions, patients). Prevent Leakage: Strict separation of training/test sets; use unbiased benchmarks [8] [7]. |
| 4. Feature Extraction | Utilize the model's "zero-shot" embeddings without further fine-tuning for initial evaluation. | Output: Gene embeddings and cell embeddings as generated by the pretrained model for downstream analysis [7]. |
| 5. Performance Evaluation | Assess using a suite of metrics, including novel biology-aware metrics. | Standard Metrics: Accuracy, F1-score, etc. Novel Metrics: scGraph-OntoRWR (biological consistency), LCAD (error severity) [7]. |
The Scientist's Toolkit: Key Research Reagents & Materials
- Table 2: Essential Components for scFM Benchmarking
| Item | Function in the Experiment |
|---|---|
| Benchmark Datasets | High-quality, annotated scRNA-seq datasets used as the ground truth for evaluating model performance on specific tasks like cell type annotation or drug response prediction [7]. |
| Single-cell Foundation Models (scFMs) | The pretrained models (e.g., Geneformer, scGPT) being evaluated. They serve as the tool for generating features or predictions from raw single-cell data [7]. |
| Baseline Models | Traditional methods (e.g., Seurat, Harmony, scVI) or simple machine learning models used as a point of comparison to quantify the added value of the complex scFMs [7]. |
| Ontology-Informed Metrics | Specialized evaluation tools like scGraph-OntoRWR and LCAD that measure whether the model's outputs are consistent with prior biological knowledge from established ontologies [7]. |
| Quantitative Systems Pharmacology (QSP) Models | Computational platforms that integrate diverse data to mechanistically simulate disease and drug effects. They are a key tool for reverse translation, helping to bridge the gap between preclinical models and human clinical outcomes [66]. |
Workflow Diagram: From Data to Decision
The Reverse Translation Cycle
Conclusion
Preventing data leakage is not a mere technicality but a fundamental requirement for credible scientific progress in scFM benchmarking and computational drug discovery. By integrating foundational understanding, rigorous methodologies, proactive troubleshooting, and stringent validation, researchers can construct benchmarks that yield truly generalizable and reliable models. The future of AI in biomedicine hinges on this integrity. Adopting these practices will accelerate the translation of computational predictions into successful clinical outcomes, ensuring that investments in R&D are built upon a foundation of reproducible and trustworthy science. The field must move towards standardized, leakage-aware benchmarking protocols, similar to the CARA initiative, to foster robust innovation and maintain scientific rigor.
References
- 1. Data splitting to avoid information leakage with DataSAIL [https://pmc.ncbi.nlm.nih.gov/articles/PMC11978981/]
- 2. PertEval-scFM: Benchmarking Single-Cell Foundation ... [https://openreview.net/forum?id=MWP9V0Ej0d]
- 3. PertEval-scFM: Benchmarking Single-Cell Foundation ... [https://icml.cc/virtual/2025/poster/43799]
- 4. Publishing neural networks in drug discovery might ... [https://jcheminf.biomedcentral.com/articles/10.1186/s13321-025-00982-w]
- 5. How to Prevent Data Leaks [https://www.upguard.com/blog/data-leak-prevention-tips]
- 6. Large-scale prediction of activity cliffs using machine and ... [https://jcheminf.biomedcentral.com/articles/10.1186/s13321-022-00676-7]
- 7. Biology-driven insights into the power of single-cell ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12492631/]
- 8. Creating Unbiased Public Benchmark Datasets with Data ... [https://arxiv.org/abs/2107.01905]
- 9. Benchmarking compound activity prediction for real-world ... [https://www.nature.com/articles/s42004-024-01204-4]
- 10. 'An Existential Crisis' for Science - Institute for Policy Research [https://www.ipr.northwestern.edu/news/2024/an-existential-crisis-for-science.html]
- 11. Replication crisis [https://en.wikipedia.org/wiki/Replication_crisis]
- 12. Reproducibility: The science communities' ticking ... [https://frontlinegenomics.com/reproducibility-the-science-communities-ticking-timebomb-can-we-still-trust-published-research/]
- 13. Article BioLLM: A standardized framework for integrating ... [https://www.sciencedirect.com/science/article/pii/S2666389925001746]
- 14. Ten simple rules for good research practice - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC9223329/]
- 15. Don't push the button! Exploring data leakage risks in ... [https://link.springer.com/article/10.1007/s10462-025-11326-3]
- 16. Data Leakage in 2025: Types, Causes, and 5 Defensive ... [https://www.venn.com/learn/dlp/data-leakage/]
- 17. Leakage and the reproducibility crisis in machine-learning- ... [https://www.sciencedirect.com/science/article/pii/S2666389923001599]
- 18. Data Leakage Prevention in AI [https://blog.qualys.com/product-tech/2025/04/18/data-leakage-prevention-in-ai]
- 19. QSPRpred: a Flexible Open-Source Quantitative Structure ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11566221/]
- 20. Single-cell foundation models: bringing artificial ... [https://www.nature.com/articles/s12276-025-01547-5]
- 21. Closing the loop: Teaching single-cell foundation models to ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12265564/]
- 22. GitHub - hansweytjens/predictive-process-monitoring- benchmarks ... [https://github.com/hansweytjens/predictive-process-monitoring-benchmarks]
- 23. Data Preprocessing in Machine Learning: Steps & Best ... [https://lakefs.io/blog/data-preprocessing-in-machine-learning/]
- 24. Mastering data preprocessing: Techniques and best ... [https://www.blog.trainindata.com/mastering-data-preprocessing-techniques/]
- 25. scDrugMap: Benchmarking Large Foundation Models for ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12083700/]
- 26. Data leakage inflates prediction performance in ... [https://www.nature.com/articles/s41467-024-46150-w]
- 27. Scalable multi-sample single-cell data analysis by Partition ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC5760091/]
- 28. Data splitting — Chemprop 2.2.1 documentation [https://chemprop.readthedocs.io/en/latest/tutorial/python/data/splitting.html]
- 29. Three-Way Split of datasets every Data Scientist should ... [https://ubiai.tools/test-and-training-set-explained-for-data-scientist/]
- 30. Mitigating Data Leakage in a WiFi CSI Benchmark for ... [https://www.mdpi.com/1424-8220/24/24/8201]
- 31. Benchmarking compound activity prediction for real-world ... [https://pubmed.ncbi.nlm.nih.gov/38834746]
- 32. AntiLeakBench: Preventing Data Contamination by ... [https://arxiv.org/abs/2412.13670]
- 33. Target-Free Compound Activity Prediction via Few-Shot ... [https://arxiv.org/abs/2311.16328]
- 34. Preventing Data Leakage in Feature Engineering - dotData [https://dotdata.com/blog/preventing-data-leakage-in-feature-engineering-strategies-and-solutions/]
- 35. Data Leakage In Machine Learning: Examples & How to ... [https://airbyte.com/data-engineering-resources/what-is-data-leakage]
- 36. Data Leakage in Machine Leaning [https://medium.com/@speaktoharisudhan/data-leakage-in-machine-leaning-c382b65f4c09]
- 37. Biology-driven insights into the power of single-cell foundation ... [https://genomebiology.biomedcentral.com/articles/10.1186/s13059-025-03781-6]
- 38. A First Investigation of Data Leakage in LLMs Across 83 ... [https://arxiv.org/html/2502.06215v1]
- 39. Tempering implementation optimism: distinguishing between ... [https://implementationsciencecomms.biomedcentral.com/articles/10.1186/s43058-025-00781-2]
- 40. Train-Test-Validation Split in 2025 [https://www.analyticsvidhya.com/blog/2023/11/train-test-validation-split/]
- 41. Data Partitioning in PySpark [https://www.geeksforgeeks.org/python/data-partitioning-in-pyspark/]
- 42. The ALCOA++ Principles for Data Integrity in Clinical Trials [https://www.quanticate.com/blog/alcoa-principles]
- 43. Virtual Screening in Lead Discovery: A Viewpoint - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC6146595/]
- 44. Hit & Lead Discovery | Hit-to-Lead Services [https://axxam.com/screening-hit-to-lead/hit-to-lead/]
- 45. BioLLM: A standardized framework for integrating and ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12365531/]
- 46. What is Automated Data Classification? 2025 Guide [https://concentric.ai/a-2025-guide-to-automated-data-classification/]
- 47. What is Data Classification? AI, Types & Best Practices ... [https://www.bizdata360.com/what-is-data-classification-ai-types-best-practices-guide-2025/]
- 48. The Best 5 Data Classification Tools in 2025 [https://numerous.ai/blog/data-classification-tools]
- 49. Data Leakage Prevention (DLP) Solutions 2025-2033 ... [https://www.datainsightsmarket.com/reports/data-leakage-prevention-dlp-solutions-1368762]
- 50. Comprehensive Overview of the Data Leakage Prevention ... [https://www.linkedin.com/pulse/comprehensive-overview-data-leakage-prevention-system-market-2025-2032-ytp9c]
- 51. Automatic Leak Test Apparatus Analysis 2025 and ... [https://www.marketreportanalytics.com/reports/automatic-leak-test-apparatus-21813]
- 52. Benchmarking Benchmark Leakage in Large Language Models [https://arxiv.org/html/2404.18824v1]
- 53. Systema: a framework for evaluating genetic perturbation ... [https://www.nature.com/articles/s41587-025-02777-8]
- 54. Benchmarking the Benchmark dataset Leakage in Large Language Models | by SACHIN KUMAR | Medium [https://medium.com/@techsachin/benchmarking-the-benchmark-dataset-leakage-in-large-language-models-c0d052ef743e]
- 55. Data Leakage in Machine Learning Models - Shelf.io [https://shelf.io/blog/preventing-data-leakage-in-machine-learning-models/]
- 56. Overview of leakage scenarios in supervised machine learning [https://journalofbigdata.springeropen.com/articles/10.1186/s40537-025-01193-8]
- 57. Data 'leaks' can sink machine learning models | Yale News [https://news.yale.edu/2024/02/28/data-leaks-can-sink-machine-learning-models]
- 58. Data Leakage And Its Effect On The Performance of An ML ... [https://www.analyticsvidhya.com/blog/2021/07/data-leakage-and-its-effect-on-the-performance-of-an-ml-model/]
- 59. Data Leakage in Machine Learning: How it can be ... [https://medium.com/data-science/data-leakage-in-machine-learning-how-it-can-be-detected-and-minimize-the-risk-8ef4e3a97562]
- 60. A comparison of computational methods for expression ... [https://genomebiology.biomedcentral.com/articles/10.1186/s13059-025-03840-y]
- 61. What is Data Leakage Prevention | Data Leak Protection ... [https://www.mimecast.com/content/data-leakage-prevention/]
- 62. Better Benchmarking Improves Drug Development ... [https://www.intelligencia.ai/better-benchmarking-elevates-pharma-decision-making/]
- 63. Extensive benchmarking of a method that estimates ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11772677/]
- 64. ISO 27002:2022 – Control 8.12 – Data Leakage Prevention [https://www.isms.online/iso-27002/control-8-12-data-leakage-prevention/]
- 65. Best Practices for Data Integrity in Pharmaceutical Industry ... [https://www.avslifesciences.com/blog-post/best-practices-for-data-integrity-in-pharmaceutical-industry-compliance]
- 66. Integrating Quantitative Clinical Pharmacology and Reverse ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC5813105/]
- 67. Bench-to-Bedside - an overview [https://www.sciencedirect.com/topics/chemistry/bench-to-bedside]